Jeder IT-Admin, der KeePass für ein Team betreibt, erzählt dieselbe Geschichte. Es beginnt mit einer gemeinsamen .kdbx-Datei auf einem Netzlaufwerk. Dann kann jemand sie nicht öffnen, weil ein Kollege sie gesperrt hat. Dann überschreibt ein Junior-Sysadmin eine Änderung, die jemand anderes eine Stunde zuvor gemacht hat. Dann verlässt ein Mitarbeiter das Unternehmen, und niemand weiß genau, auf welche Passwörter er Zugriff hatte.
KeePass ist ein wirklich hervorragendes Werkzeug — für eine Person. Sobald es von einem Team genutzt wird, verwaltet man keine Passwörter mehr. Man verwaltet eine einzelne Datei.
Wichtige Erkenntnisse
KeePass ist hervorragend für Einzelpersonen, aber strukturell ungeeignet für Teams. Sobald ein zweiter Benutzer hinzukommt, gehen Echtzeit-Synchronisation, granulare Zugriffssteuerung und Audit-Trails verloren — die drei Dinge, die Credential-Breaches und Compliance-Verstöße verhindern.
- Multi-User-Synchronisation ist manuell und fehleranfällig. Gleichzeitige Bearbeitungen an einer gemeinsamen .kdbx-Datei führen zu Datenverlust. Das „Last-Writer-Wins"-Problem skaliert linear mit der Teamgröße. Es gibt keinen Merge, keine Konflikterkennung und keine Warnung.
- Die Zugriffssteuerung ist binär. Jeder, der das Masterpasswort benötigt, erhält vollen Zugriff auf alle Zugangsdaten. Es gibt kein Konzept für „dieser Benutzer kann Cloud-Zugangsdaten lesen, aber keine Datenbankpasswörter". Beim Offboarding müssen alle Zugangsdaten rotiert werden, die die Person möglicherweise gesehen hat.
- KeePass erzeugt keine Audit-Logs. Es lässt sich nicht nachweisen, wer wann und von wo auf bestimmte Zugangsdaten zugegriffen hat. Dies verstößt gegen SOC 2 CC6.1, GDPR Artikel 32, NIS2, ISO 27001 und PCI DSS 4.0 — jedes moderne Compliance-Framework.
- Die operativen Kosten summieren sich schnell. Sync-Konflikte, manuelles Offboarding, Credential-Rotation und Audit-Lücken erzeugen einen administrativen Overhead, der mit der Teamgröße wächst.
- Die Lösung ist ein zweckgebauter Tresor mit RBAC, AD-Integration und automatisierten Audit-Trails. Keine größere Tabelle, kein besseres Filesharing-Tool — ein Credential-Manager, der für Teams unter Compliance-Anforderungen entwickelt wurde.
Die Attraktivität von KeePass für kleine Unternehmen
KeePass ist aus drei völlig rationalen Gründen für KMU attraktiv: Es kostet nichts, speichert Daten lokal und wurde von der Open-Source-Community seit über zwei Jahrzehnten auditiert. Für ein Fünf-Personen-Unternehmen ohne Compliance-Verpflichtungen und mit einem einzelnen IT-Generalisten sind das echte Vorteile.
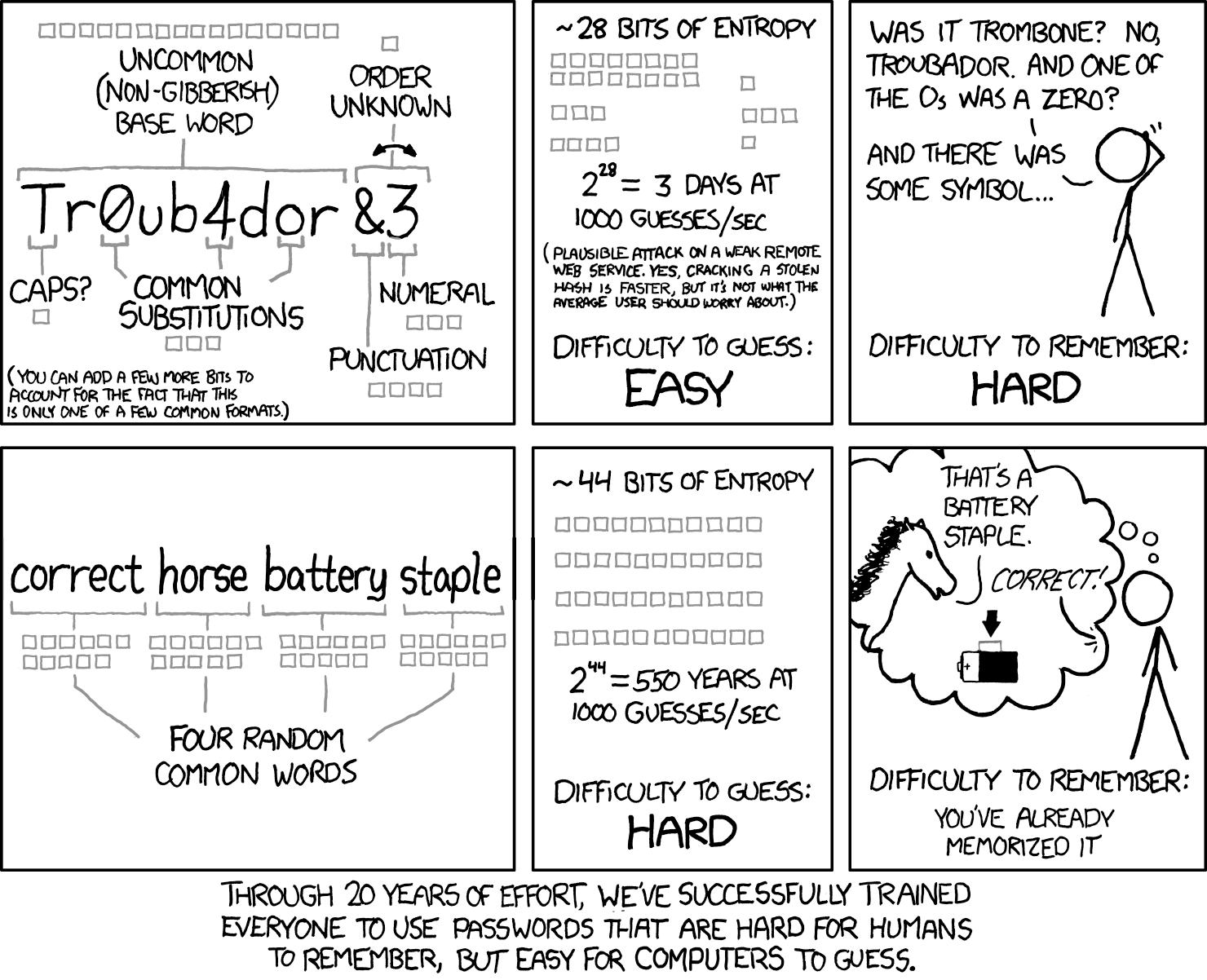
Die Verschlüsselung ist solide. KeePass 2.x verwendet standardmäßig AES-256, mit optionaler ChaCha20-Unterstützung — letztere ist schneller auf mobiler Hardware, wo keine AES-Hardwarebeschleunigung verfügbar ist. Das .kdbx-Format ist gut dokumentiert, portabel und wird nicht verschwinden.
KeePass bleibt ein bedeutender Teil der Consumer-Adoption-Kurve, besonders unter technisch versierten Nutzern, die Cloud-Diensten misstrauen. Das Enterprise-Segment (wo Compliance-Audits, Multi-Team-Zugriff und Audit-Logging obligatorisch sind) ist jedoch fast vollständig auf zweckgebaute Lösungen umgestiegen.
Was ist AES-256?
AES-256 (Advanced Encryption Standard mit 256-Bit-Schlüssel) ist eine symmetrische Blockchiffre, die 2001 vom NIST standardisiert wurde (FIPS 197). Sie arbeitet mit 128-Bit-Blöcken über 14 Runden von Substitution, Permutation und Schlüsselmischung. Die 256-Bit-Schlüssellänge macht Brute-Force-Angriffe mit aktueller und absehbarer Hardware rechnerisch undurchführbar. AES-256 ist der Verschlüsselungsstandard in TLS, Festplattenverschlüsselung (BitLocker, FileVault) und den meisten Enterprise-Credential-Managern — einschließlich Passwork, das es clientseitig anwendet, bevor Daten das Gerät verlassen.
Was ist ChaCha20?
ChaCha20 ist eine Stromchiffre, die 2008 von Daniel J. Bernstein als schnellere, hardwareunabhängige Alternative zu AES entwickelt wurde. Sie wendet 20 Runden von ARX-Operationen (Add, Rotate, XOR) auf einen 256-Bit-Schlüssel und eine 96-Bit-Nonce an und erzeugt einen Keystream, der mit dem Klartext XOR-verknüpft wird. Anders als AES ist ChaCha20 nicht auf Hardware-Beschleunigungsbefehle angewiesen — wodurch es auf Geräten ohne AES-NI-Unterstützung erheblich schneller ist, wie etwa ältere mobile CPUs und eingebettete Systeme. Es wird weitverbreitet in TLS 1.3 eingesetzt (gepaart mit Poly1305 als ChaCha20-Poly1305) und ist die Standard-Chiffre in WireGuard. KeePass 2.x unterstützt ChaCha20 als Alternative zu AES-256 für die Datenbankverschlüsselung, weshalb es auf Low-End-Android- und iOS-Hardware besser performt.
Was ist eine .kdbx-Datei?
.kdbx ist das binäre Datenbankformat, das von KeePass 2.x und seinen Forks verwendet wird. Die Datei speichert alle Zugangsdaten in einem verschlüsselten Container — geschützt durch AES-256 oder ChaCha20 — und wird mit einem Masterpasswort, einer Schlüsseldatei oder beidem entsperrt. Das Format ist in sich geschlossen und portabel: Der gesamte Credential-Speicher befindet sich in einer einzigen Datei ohne Server, ohne Sync-Engine und ohne Benutzerkonten. KDBX 4.0 (eingeführt in KeePass 2.35) fügte Argon2 als Key-Derivation-Funktion hinzu und ersetzte AES-KDF, wodurch die Widerstandsfähigkeit gegen GPU-basierte Brute-Force-Angriffe erheblich erhöht wurde. Das Single-File-Design macht .kdbx hervorragend für den Einzeleinsatz — und strukturell ungeeignet für gleichzeitigen Multi-User-Zugriff.
Die „KeePass-Skalierungsfalle": Wenn kostenlos teuer wird

KeePass wurde als Single-User-Anwendung konzipiert. Die Multi-User-Dokumentation räumt dies direkt ein — die offizielle KeePass-Hilfeseite für mehrere Benutzer beschreibt Workarounds, keine nativen Funktionen. Wenn Sie eine .kdbx-Datei auf ein Netzlaufwerk legen und fünf Personen Zugriff geben, haben Sie ein System gebaut, das irgendwann versagen wird. Hier ist genau, wie.
Das Last-Writer-Wins-Problem
KeePass hat keine Echtzeit-Sync-Engine. Wenn zwei Benutzer dieselbe Datenbankdatei gleichzeitig öffnen, hält jeder eine lokale Kopie im Speicher. Wenn Benutzer A speichert, wird die Datei aktualisiert. Wenn Benutzer B dreißig Sekunden später speichert, überschreibt seine Version die Änderungen von Benutzer A vollständig. Es gibt keinen Merge, keine Konflikterkennung und keine Warnung.
KeePass bietet zwar eine manuelle „Synchronisieren"-Funktion, die zwei .kdbx-Dateien zusammenführen kann — aber sie erfordert eine bewusste Aktion des Benutzers und funktioniert nur, wenn beide Versionen verfügbar sind. Auf einem Netzlaufwerk, wo die Datei beim Speichern überschrieben wird, ist diese zweite Version bereits verschwunden.
Alles-oder-Nichts-Zugriff
KeePass hat ein Masterpasswort (oder eine Schlüsseldatei) pro Datenbank. Jeder, der Zugriff benötigt, erhält denselben Schlüssel. Es gibt kein Konzept für „dieser Benutzer kann die Cloud-Server-Zugangsdaten lesen, aber nicht die Datenbankpasswörter". Sie können separate .kdbx-Dateien für verschiedene Zugriffsebenen erstellen, aber dann verwalten Sie mehrere Dateien und mehrere Sync-Prozesse — und Sie haben immer noch keinen Audit-Trail.
RBAC (rollenbasierte Zugriffssteuerung) — die Möglichkeit zu definieren, was jeder Benutzer oder jede Gruppe sehen und tun kann — existiert in der Architektur von KeePass schlicht nicht. Es ist eine Designentscheidung für ein Single-User-Tool.
Das Offboarding
Wenn ein Mitarbeiter mit Zugriff auf die gemeinsame KeePass-Datenbank Ihre Organisation verlässt, ist die korrekte Sicherheitsreaktion, alle Zugangsdaten zu rotieren, die er möglicherweise gesehen hat. Alle. Da Sie kein Log darüber haben, worauf er zugegriffen hat, können Sie die Rotation nicht eingrenzen — Sie müssen vom Worst-Case ausgehen.
Bei einer Datenbank mit 200 Einträgen ist das ein voller Arbeitstag. Bei einer Datenbank mit 800 Einträgen über Produktionssysteme, SaaS-Tools und Kundenumgebungen hinweg ist es ein mehrtägiger Incident. Und das passiert jedes Mal, wenn jemand geht.

Die rollenbasierten Tresore von Passwork ermöglichen es, den Zugriff für einen ausscheidenden Mitarbeiter mit einer einzigen Aktion zu widerrufen. Erfahren Sie, wie es funktioniert
Sicherheit vs. Compliance: Die regulatorische Landschaft 2026

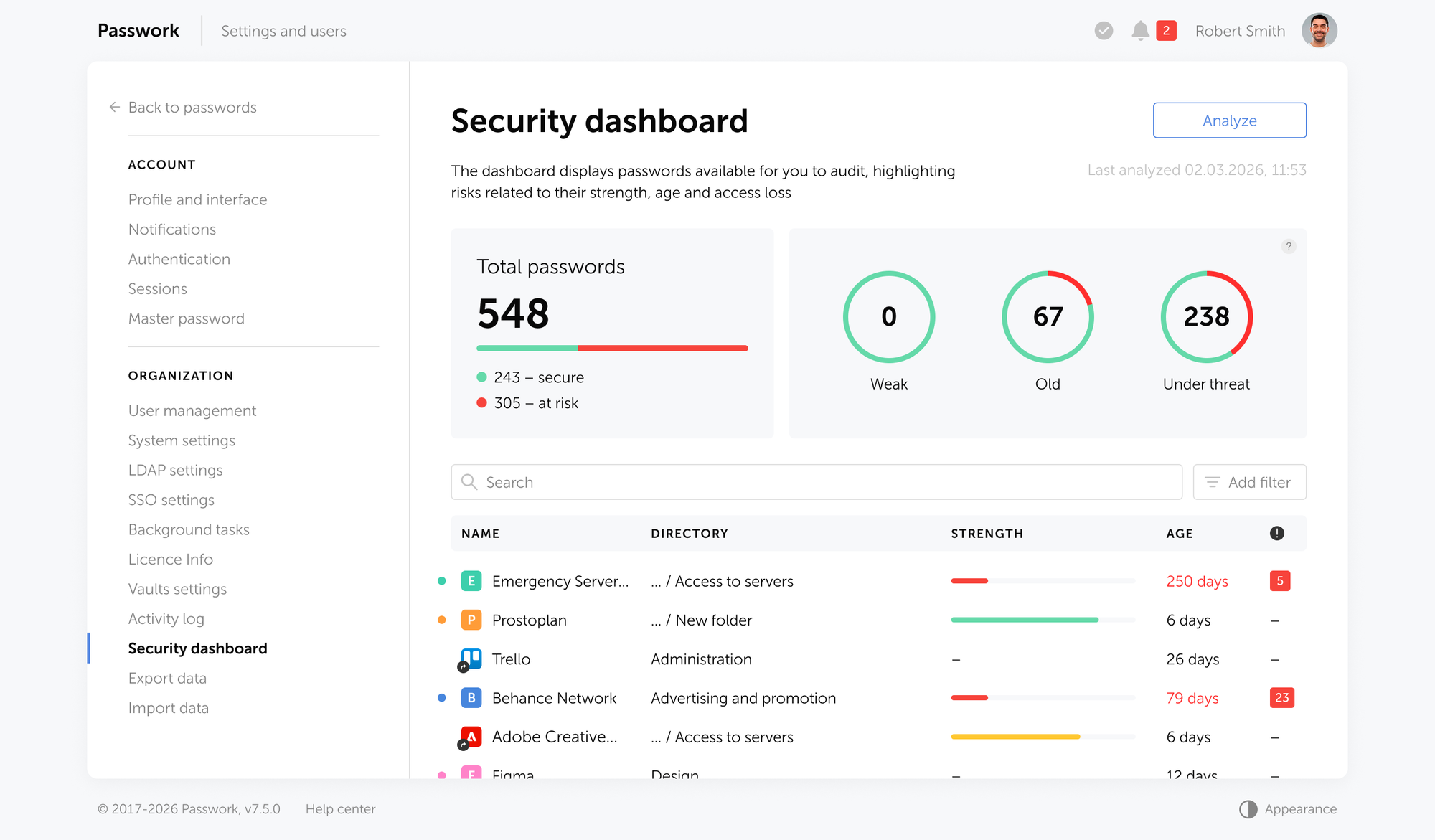
Die Verschlüsselung von KeePass ist wirklich stark. AES-256 mit einem gut gewählten Masterpasswort ist nicht der Schwachpunkt. Der Schwachpunkt ist, dass KeePass keine Nachweise darüber produziert, was innerhalb der Datenbank passiert ist — und 2026 sind diese Nachweise das, wonach Auditoren fragen.
Was GDPR Artikel 32 verlangt
GDPR Artikel 32 schreibt „geeignete technische und organisatorische Maßnahmen" vor, um ein dem Risiko angemessenes Sicherheitsniveau zu gewährleisten. Für das Credential-Management umfasst die Arbeitsinterpretation von Artikel 32 Verschlüsselung im Ruhezustand, Zugriffskontrollen und — entscheidend — die Fähigkeit nachzuweisen, dass die Zugriffskontrollen funktionieren. Dieser letzte Teil erfordert Logs.
Eine KeePass-Datenbank kann nicht sagen, wer sie geöffnet hat, wann, von welchem Rechner oder was angesehen wurde. Wenn ein Regulator Sie auffordert nachzuweisen, dass der Zugriff auf personenbezogene Zugangsdaten angemessen eingeschränkt war, ist eine .kdbx-Datei keine Antwort.
NIS2-Richtlinie: Zugriffssteuerung und Incident Response
Die NIS2-Richtlinie (seit Oktober 2024 für EU-Organisationen gültig) schreibt vor, dass Betreiber wesentlicher Dienste und wichtige Einrichtungen „erweiterte Zugriffssteuerung" implementieren und detaillierte Logs über den Zugriff auf kritische Assets führen müssen. Für das Credential-Management bedeutet das:
- Rollenbasierte Zugriffssteuerung (RBAC) mit Authentifizierung pro Benutzer
- Unveränderliche Audit-Logs aller Credential-Zugriffe
- Die Fähigkeit, den Zugriff beim Ausscheiden eines Mitarbeiters sofort zu widerrufen
Eine gemeinsam genutzte KeePass-Datei mit einem einzigen Masterpasswort verletzt alle drei Anforderungen. Das Neuschlüsseln der gesamten Datenbank, wenn jemand geht, ist kein „sofortiger Widerruf" — es ist ein Workaround, der administrativen Overhead erzeugt und das Risiko menschlicher Fehler erhöht.
ISO 27001:2022 und Anforderungen an die Zugriffssteuerung
ISO 27001 Anhang A.8.2 (Zugriffssteuerung) und A.8.15 (Protokollierung) verlangen von Organisationen, Kontrollen zu implementieren, die den Zugang zu Informationen auf autorisierte Benutzer beschränken und Aufzeichnungen über den Zugriff führen. Für Credential-Repositories bedeutet das:
- Granulare Zugriffsberechtigungen, die an Jobrollen gebunden sind
- Audit-Trails, die zeigen, wer wann und von wo auf was zugegriffen hat
- Automatisierte Durchsetzung des Prinzips der geringsten Berechtigung
KeePass bietet nichts davon. Eine Datenbank, die von Teammitgliedern mit einem einzigen Passwort geteilt wird, ist das Gegenteil von geringster Berechtigung — es ist maximale Berechtigung für alle.
PCI DSS 4.0: Schutz von Zahlungskartendaten
Wenn Ihre Organisation Zahlungskartendaten verarbeitet, schreibt PCI DSS 4.0 Anforderung 7.1 vor, dass der Zugriff auf Karteninhaberdaten auf Personal mit legitimem geschäftlichem Bedarf beschränkt werden muss. Anforderung 10.2.1 erfordert die Protokollierung aller Zugriffe auf Systeme, die Karteninhaberdaten enthalten, einschließlich Benutzer-ID, Datum, Uhrzeit und Art des Zugriffs.
Eine KeePass-Datenbank, die Payment-Gateway-API-Schlüssel oder Datenbankzugangsdaten speichert, kann diese Anforderungen nicht erfüllen. Es gibt keine Authentifizierung pro Benutzer, keinen Audit-Trail und keine Möglichkeit, einem PCI-Auditor nachzuweisen, dass der Zugriff auf autorisiertes Personal beschränkt war.
SOC 2 Type II und CC6.1
SOC 2 Trust Services Criteria CC6.1 verlangt, dass der logische Zugang zu Systemen, die sensible Daten speichern, auf autorisierte Benutzer beschränkt und der Zugriff protokolliert wird. Eine gemeinsam genutzte KeePass-Datenbank mit einem einzigen Masterpasswort erfüllt beide Bedingungen nicht. Es gibt keine Authentifizierung pro Benutzer und kein Log.
Dies ist kein theoretisches Risiko. Auditoren fragen bei SOC 2 Type II-Bewertungen nach Zugriffs-Logs. „Wir verwenden KeePass" beendet dieses Gespräch ungünstig.
NIST SP 800-63B (Revision 4)
NIST SP 800-63B, finalisiert im August 2025, empfiehlt eine Mindestpasswortlänge von 15 Zeichen für gemerkte Geheimnisse und rät ausdrücklich von obligatorischer periodischer Rotation ab, zugunsten einer durch Breaches ausgelösten Rotation. KeePass kann konforme Passwörter speichern — aber es kann die Richtlinie nicht durchsetzen, keine Compliance-Berichte erstellen und einem Auditor nicht nachweisen, dass die Richtlinie befolgt wurde.
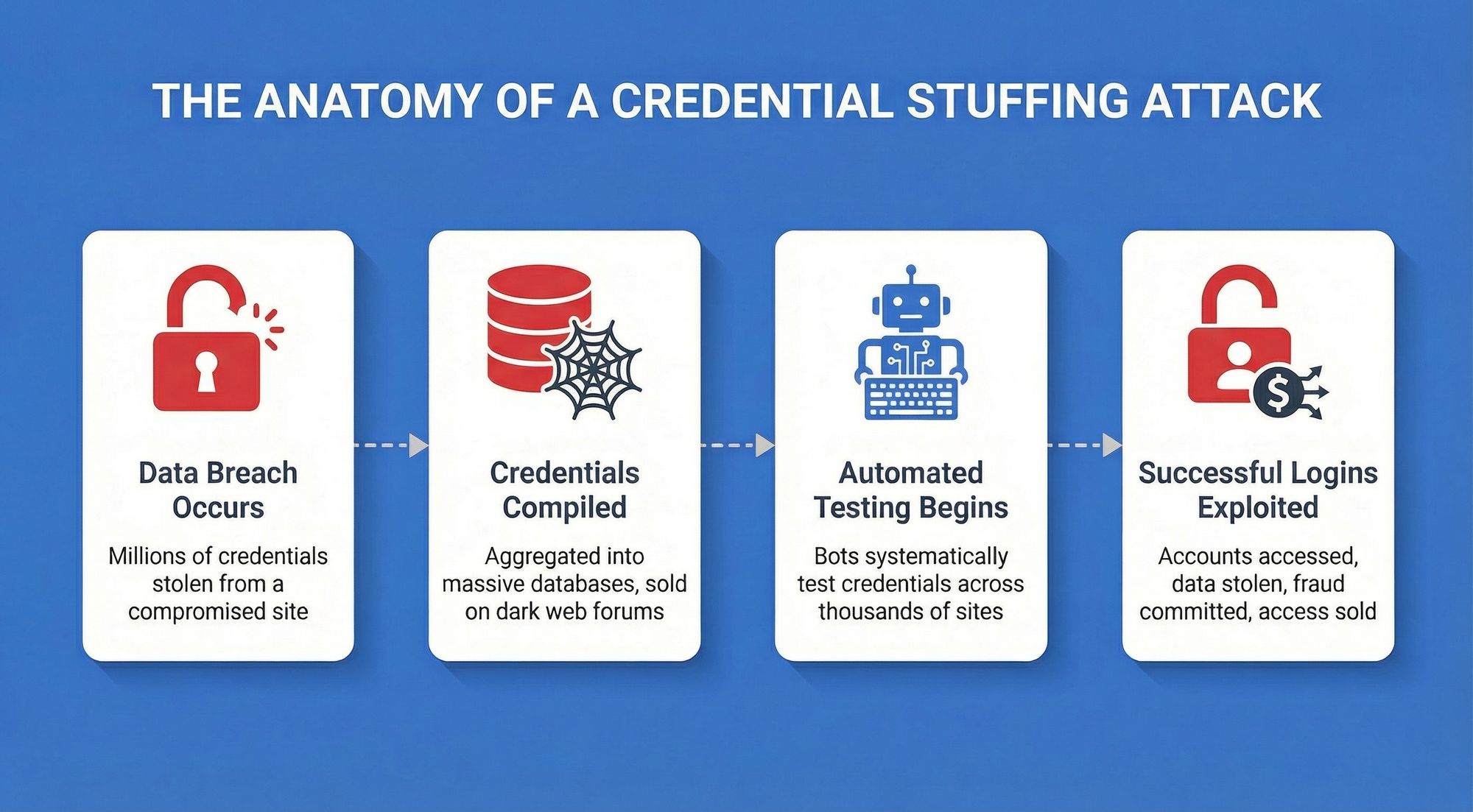
Das Ausmaß der Bedrohung
Die Zahlen machen das Compliance-Argument konkret. Laut dem IBM 2025 Cost of a Data Breach Report erreichten die durchschnittlichen Breach-Kosten für Unternehmen mit weniger als 500 Mitarbeitern 3,31 Millionen Dollar. Credential-Kompromittierung gehört konstant zu den häufigsten initialen Angriffsvektoren. Ein Compliance-Verstoß zusätzlich zu einem Breach verstärkt den finanziellen Schaden durch regulatorische Bußgelder und Sanierungskosten.
Die Reifekurve der Passwortsicherheit für KMU
Die meisten KMU durchlaufen drei erkennbare Stufen. Diese Progression zu benennen hilft Teams zu identifizieren, wo sie stehen und wie der nächste Schritt tatsächlich aussieht.
- Stufe 1 — Excel/gemeinsames Dokument. Zugangsdaten in einer Tabelle, oft auf einem gemeinsamen Laufwerk oder in E-Mail-Threads. Keine Verschlüsselung. Keine Zugriffssteuerung. Vollständig auditierbar auf die denkbar schlechteste Art: Jeder mit der Datei kann alles sehen.
- Stufe 2 — KeePass. Verschlüsselte Datei, starke Kryptographie, keine Kosten. Eine echte Verbesserung gegenüber Stufe 1. Geeignet für Einzelpersonen und sehr kleine Teams ohne Compliance-Anforderungen. Bricht bei mehr als fünf Benutzern zusammen, bei Audits oder wenn jemand geht.
- Stufe 3 — Unternehmens-Tresor. Zweckgebautes Multi-User-Credential-Management mit RBAC, AD/LDAP-Integration, Audit-Logs pro Benutzer, MFA-Durchsetzung und automatisiertem Offboarding. Hier müssen Teams mit Compliance-Verpflichtungen, mehr als zehn Benutzern oder jeglichen kundenorientierten Sicherheitsanforderungen sein.
Die Falle ist, bei Stufe 2 zu bleiben, nachdem sie nicht mehr passt. Die Kosten dieser Verzögerung sind der administrative Overhead, das Incident-Risiko und die Audit-Findings.
Der 5-Punkte-KeePass-Stresstest für Ihr Unternehmen
Gehen Sie diese fünf Fragen mit Ihrem aktuellen Setup durch. Jedes „Ja" ist ein Signal, dass KeePass Risiken erzeugt, die Ihr Team möglicherweise nicht eingepreist hat.
- Haben Sie mehr als 5 Benutzer, die auf die gemeinsame Datenbank zugreifen?
Über fünf gleichzeitige Benutzer werden Sync-Konflikte zu einem fast täglichen Ereignis. Das „Last-Writer-Wins"-Problem skaliert linear mit der Teamgröße. - Können Sie nachweisen, wer wann auf bestimmte Zugangsdaten zugegriffen hat?
Wenn ein Kunde fragt, welcher Ihrer Mitarbeiter letzten Dienstag auf seine Systemzugangsdaten zugegriffen hat, können Sie antworten? KeePass kann diese Aufzeichnung nicht erstellen. Ein Unternehmens-Tresor mit Audit-Logging kann es. - Wird die Datenbank auf einem gemeinsamen Laufwerk, Dropbox oder ähnlichem gespeichert?
Cloud-Sync-Tools wie Dropbox fügen ihre eigene Konfliktlösung zusätzlich zu der von KeePass hinzu — was bedeutet, dass Sie mit mehreren.kdbx-Versionen enden können, ohne zuverlässig zu wissen, welche aktuell ist. Netzlaufwerke haben das oben beschriebene Dateisperrproblem. - Wie lange dauert es, den Zugriff für einen ehemaligen Mitarbeiter vollständig zu widerrufen?
Wenn die Antwort lautet „wir ändern das Masterpasswort und rotieren dann alles, was er möglicherweise gesehen hat", beschreiben Sie einen mehrstündigen Incident, der jedes Mal passiert, wenn jemand geht. Mit Zugriffssteuerung pro Benutzer ist der Widerruf eine einzige Aktion. - Schützt MFA den Tresor selbst?
KeePass unterstützt Schlüsseldateien als zweiten Faktor, aber die Verteilung und Verwaltung dieser Schlüsseldateien über ein Team hinweg ist ein eigenes operatives Problem. Native MFA-Integration — TOTP, Hardware-Keys, SSO — erfordert ein zweckgebautes Tool.
Wenn Sie die Fragen 2 und 5 mit „Nein" beantwortet haben oder die Fragen 1, 3 und 4 mit „Ja", ist Ihr Team über KeePass hinausgewachsen.

Wie verwalten Sie den Credential-Zugriff, wenn Ihr Team über fünf Personen hinaus skaliert? Passwork übernimmt das Multi-Team-Credential-Management mit RBAC, Audit-Logging und Echtzeit-Sync — ohne den operativen Overhead. Passwork kostenlos testen
Über KeePass hinaus: Auswahl einer Unternehmens-Zugriffsverwaltungslösung

Die Kriterien für einen teamtauglichen Credential-Manager sind nicht kompliziert, aber sie sind nicht verhandelbar, sobald Sie in irgendeinem Umfang oder unter irgendeinem Compliance-Framework operieren.
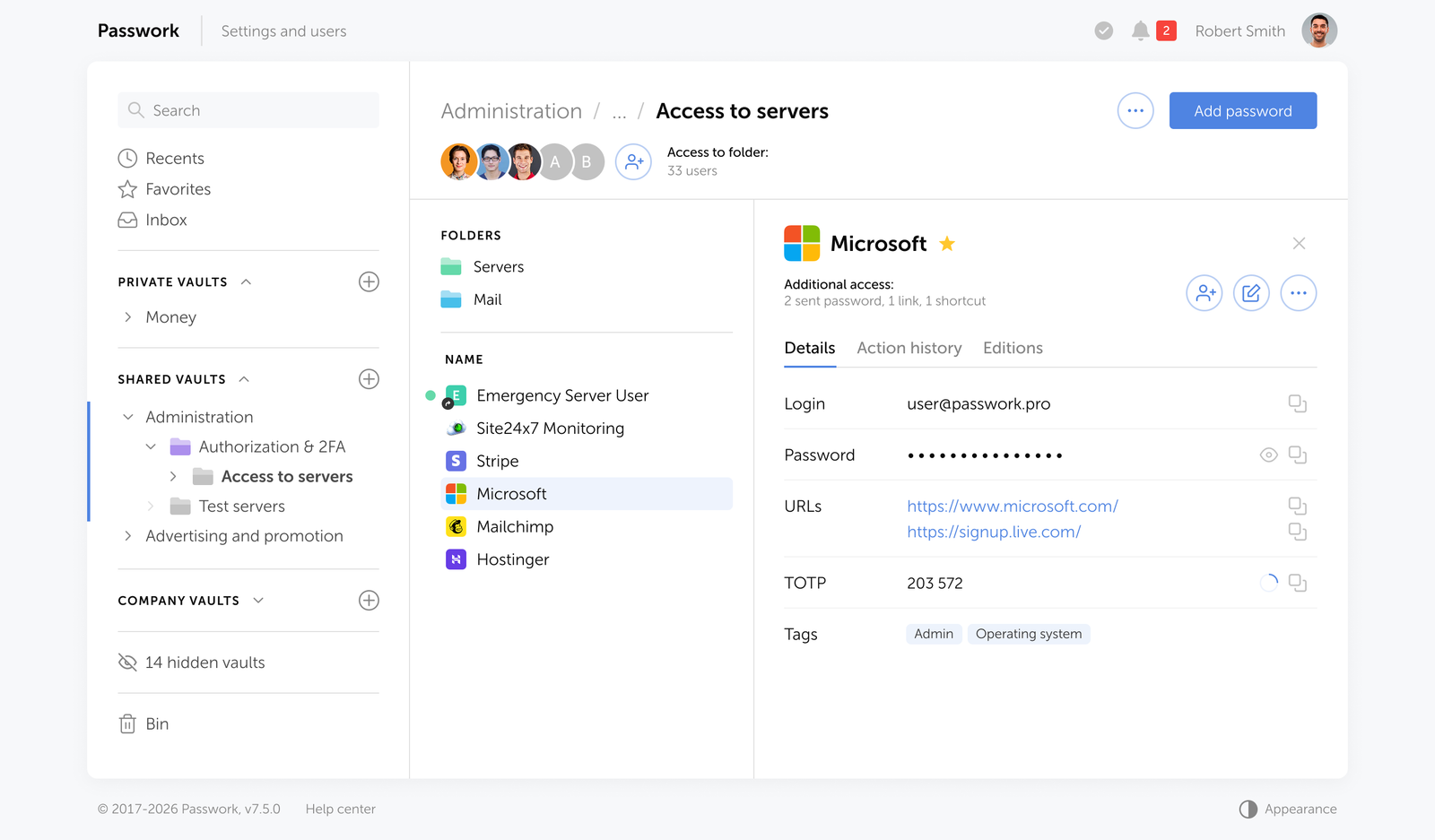
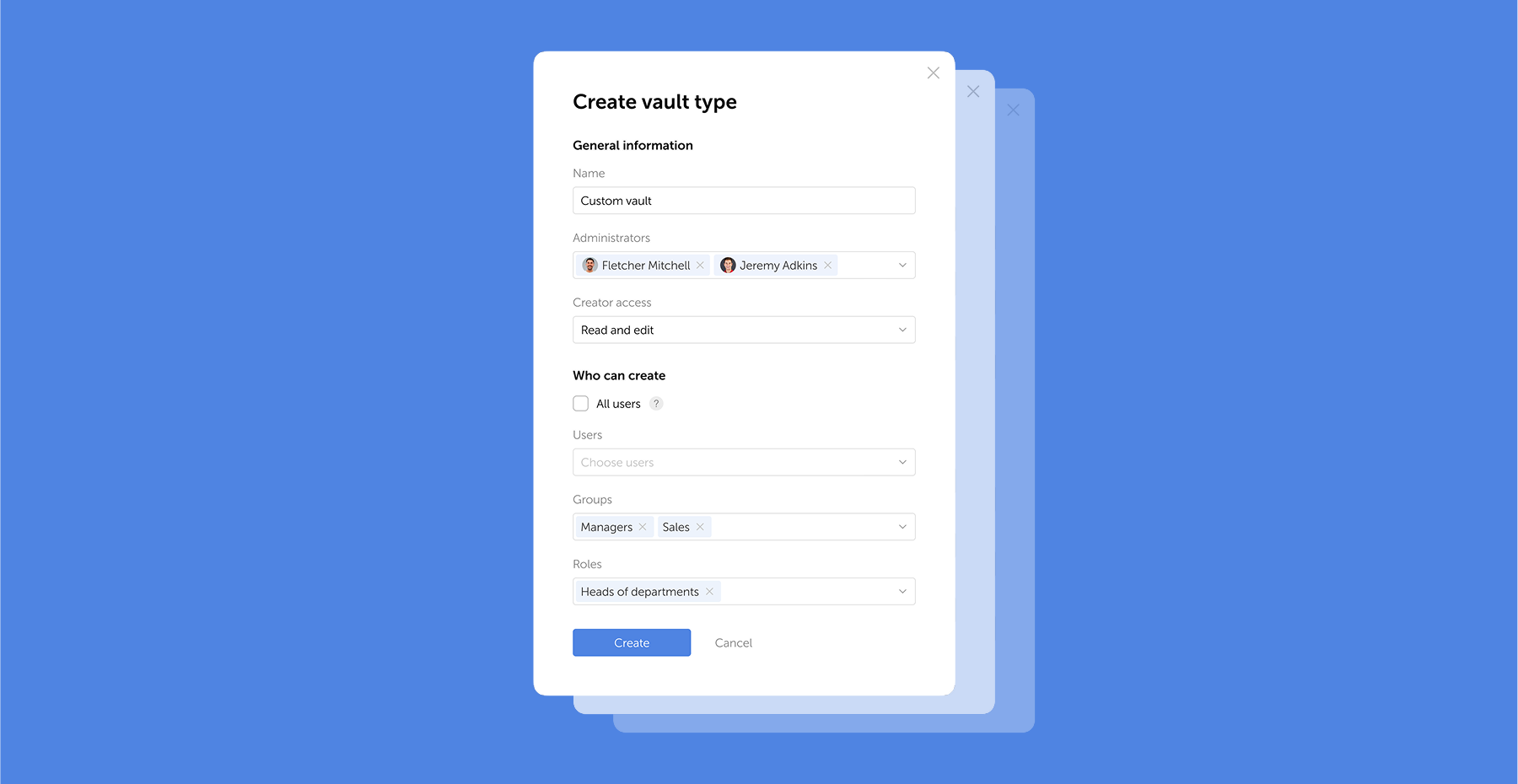
Gemeinsam genutzte Tresore mit granularen Berechtigungen
Jedes Team oder Projekt sollte seinen eigenen Tresor haben. Einzelne Benutzer erhalten Zugriff auf die Tresore, die sie benötigen, auf der Berechtigungsebene, die sie benötigen (Lesen, Schreiben, Admin). Wenn sich die Rolle einer Person ändert, aktualisieren Sie ihre Tresor-Mitgliedschaft — nicht das Masterpasswort. Das ist rollenbasierte Zugriffssteuerung (RBAC), und sie ist die Grundlage der Compliance. KeePass hat kein Äquivalent.
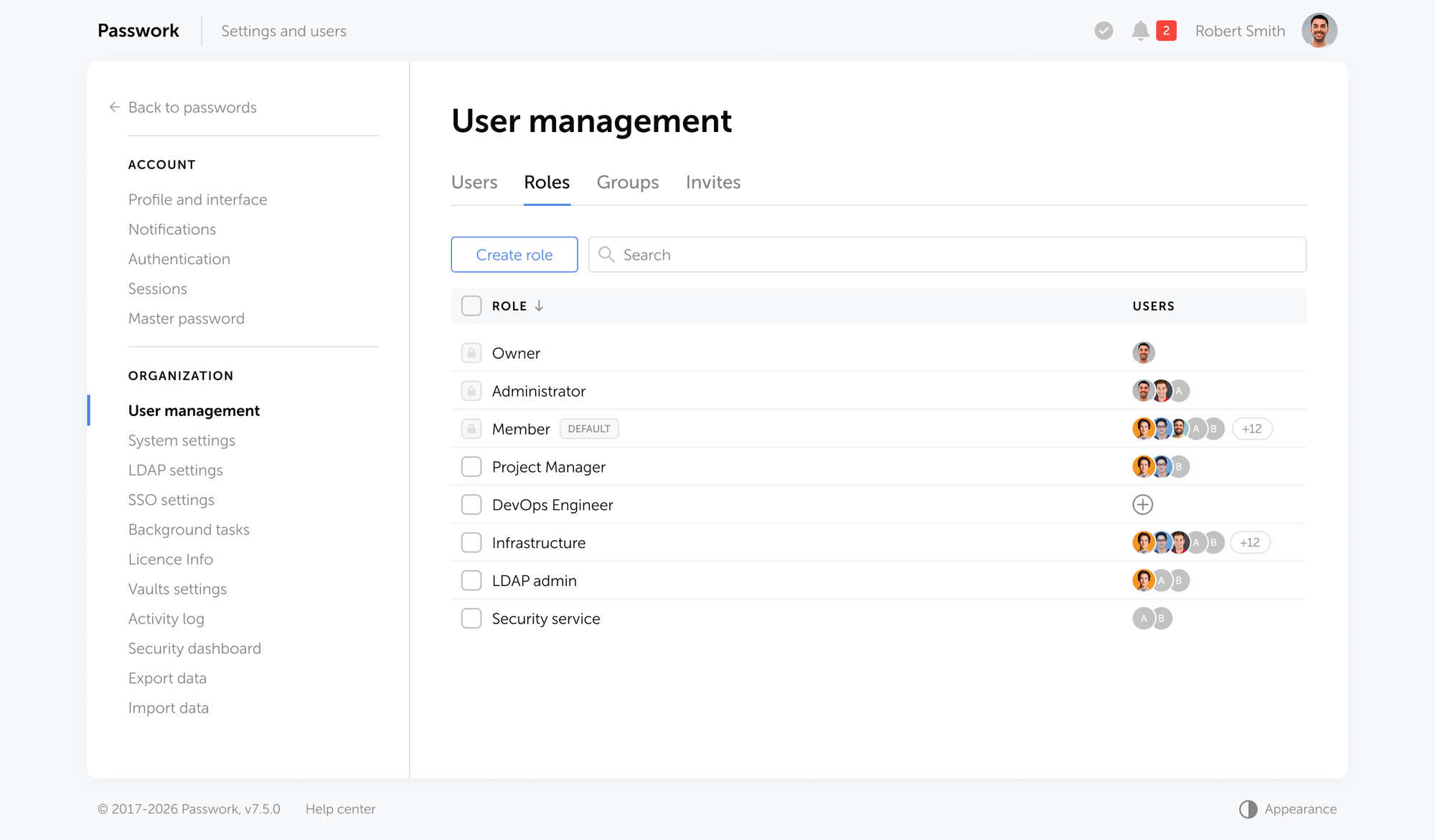
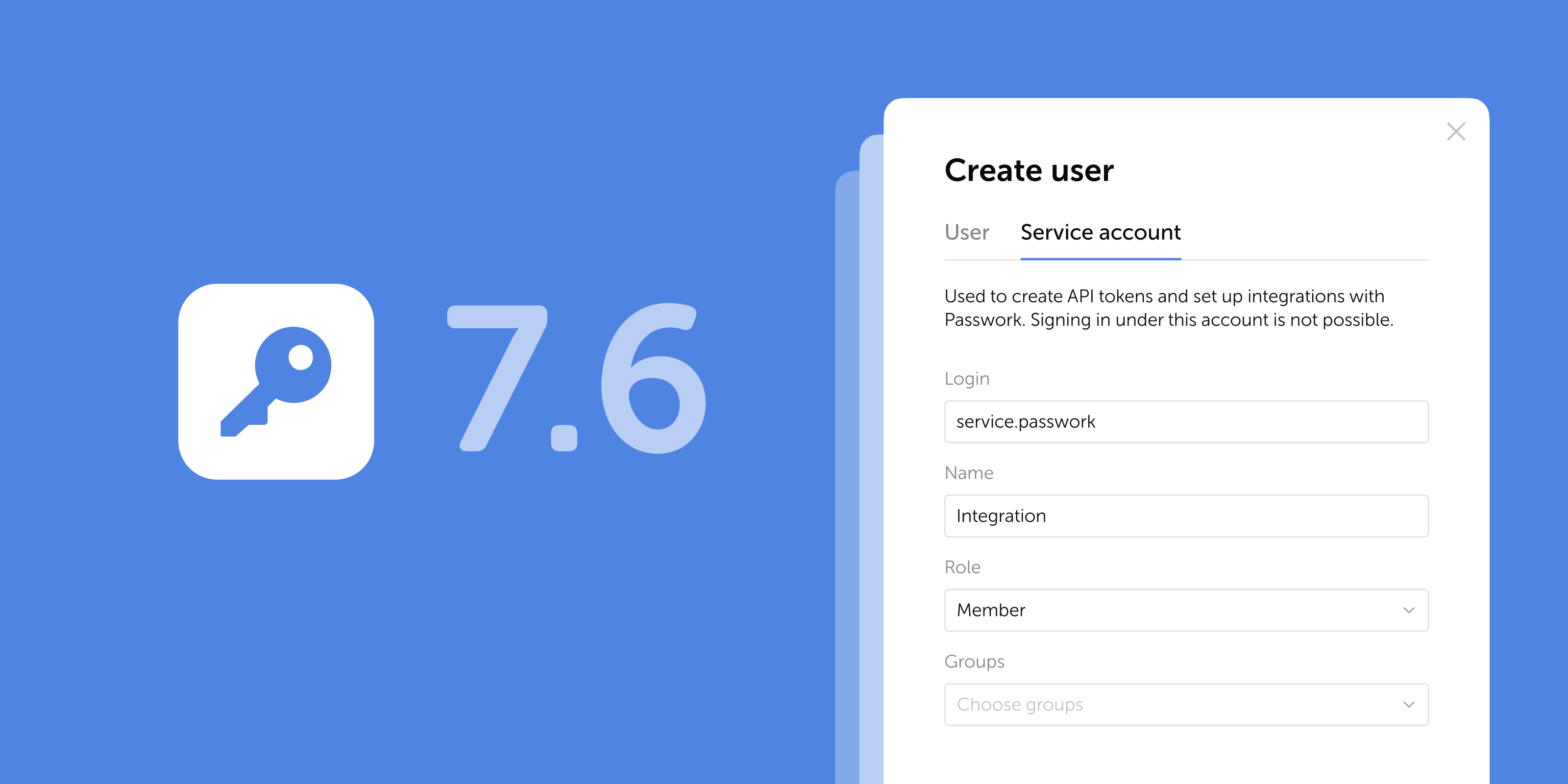
Passwork weist Gruppen Berechtigungen zu, sodass ein Entwickler, der dem DevOps-Team beitritt, automatisch den Tresor-Zugriff des Teams erbt. Wenn er geht, widerrufen Sie ihn einmal.
RBAC mit Ihrem Verzeichnis verknüpft
AD/LDAP-Integration bedeutet, dass Benutzer-Provisioning und -Deprovisioning automatisch erfolgen. Wenn der Admin ein Konto in Active Directory terminiert, geht der Tresor-Zugriff damit. Kein manueller Schritt, keine Lücke. Passwork integriert nativ mit Active Directory und LDAP, sodass Ihr Credential-Zugriff Ihrer Organisationsstruktur folgt — nicht umgekehrt.
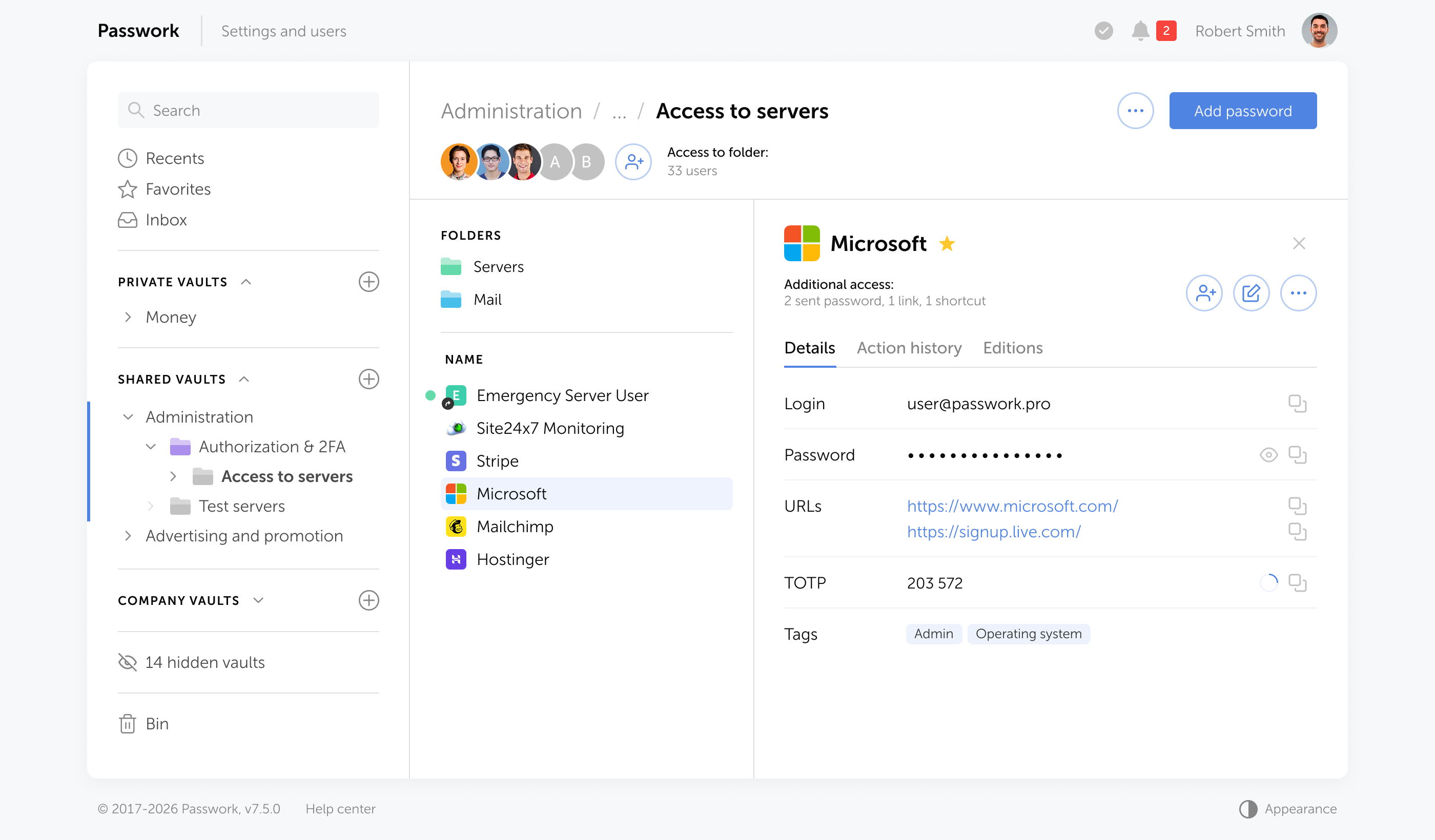
Audit-Logs pro Benutzer
Jede Credential-Ansicht, -Kopie, -Bearbeitung und -Freigabe sollte mit Zeitstempel und Benutzeridentität protokolliert werden. Dies ist die Aufzeichnung, die SOC 2 CC6.1 erfüllt und die GDPR Artikel 32-Rechenschaftspflicht unterstützt. KeePass produziert keine Logs.
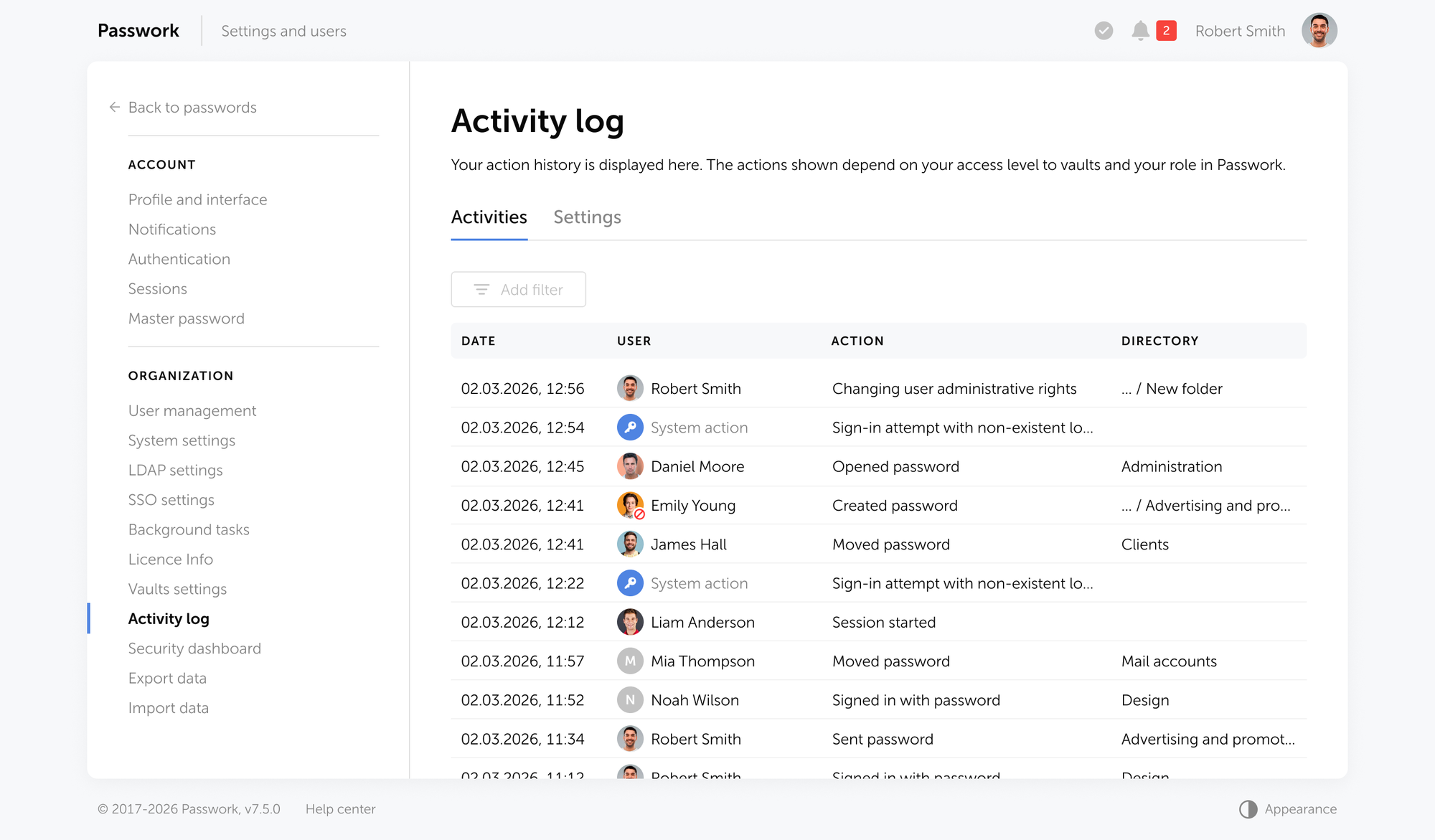
Passwork führt einen vollständigen Audit-Trail jeder Aktion, exportierbar für Compliance-Überprüfungen und Incident-Untersuchungen.
MFA-Durchsetzung auf Tresor-Ebene
Nicht optional, keine Benutzer-Präferenz — durch Richtlinie durchgesetzt, mit Unterstützung für TOTP, Hardware-Token und SAML SSO. KeePass unterstützt Schlüsseldateien, was keine MFA ist. Passwork erzwingt MFA auf Tresor-Ebene, mit Unterstützung für mehrere Authentifizierungsmethoden, die an Ihren Identity-Provider gebunden sind.
Autofill und Browser-Integration
Ein moderner Credential-Manager integriert sich mit Browsern und CLI-Tools, um Passwörter automatisch auszufüllen und Secrets in Deployment-Pipelines einzuspeisen. KeePass hat Browser-Plugins, aber sie werden von der Community gepflegt und haben nicht das Sicherheitsmodell eines zentralisierten Tresors. Passwork bietet native Browser-Erweiterungen und CLI-Tools, die Zugangsdaten on-demand aus Ihrem Tresor abrufen, mit vollständigem Audit-Logging jeder Autofill-Aktion.
Zero-Knowledge-Architektur
Ihre Credential-Daten sollten clientseitig verschlüsselt werden, bevor sie jemals den Server erreichen. Das bedeutet, der Server (ob selbstgehostet oder Cloud) kann Ihre Zugangsdaten nicht entschlüsseln. Es ist eine Garantie, kein Versprechen. KeePass verschlüsselt lokal, bietet aber keine Team-Zusammenarbeit ohne manuelles Filesharing. Passwork verwendet clientseitige AES-256-Verschlüsselung mit Zero-Knowledge-Architektur: Zugangsdaten werden vor der Übertragung verschlüsselt, verschlüsselt auf dem Server gespeichert und nur auf autorisierten Clients entschlüsselt.
Selbstgehostet oder Cloud, Ihre Wahl
Einige KMU haben regulatorische oder vertragliche Gründe, Credential-Daten on-premises zu halten. Ein Tool, das echtes Self-Hosting bietet, gibt Ihnen die Kontrolle, die KeePass bietet, ohne die operativen Einschränkungen. Passwork ist als Cloud-Passwort- und Secrets-Manager und als selbstgehostete Deployment auf Ihrer eigenen Infrastruktur verfügbar, mit vollständiger AES-256-Verschlüsselung und Zero-Knowledge-Architektur. Ihre Daten verlassen nie Ihre Kontrolle.
KeePass vs. Passwork: Funktionsvergleich
| Funktion | KeePass | Passwork |
|---|---|---|
| Multi-User-Sync | Manuell / fehleranfällig | Echtzeit, konfliktfrei |
| Granulare Berechtigungen (RBAC) | Keine | Pro Benutzer, pro Tresor |
| Audit-Logs | Keine | Vollständiges Aktivitätslog pro Benutzer |
| MFA-Durchsetzung | Nur Schlüsseldatei | TOTP, SSO, Hardware-Keys, Passkeys, Biometrie |
| AD/LDAP-Integration | Keine | Nativ |
| Automatisiertes Offboarding | Keines | Widerruf mit einer Aktion |
| Autofill und Browser-Integration | Community-Plugins | Native Erweiterungen |
| Zero-Knowledge-Verschlüsselung | Nur lokal | Clientseitig + Server |
| SIEM-Integration | Keine | syslog, REST API |
| Compliance-Nachweise | Keine | Exportierbare Audit-Berichte |
| Self-Hosting-Option | Nur dateibasiert | Volle Infrastrukturkontrolle |
Der Unterschied ist architektonisch. Wenn Ihr Team über fünf Personen hinauswächst, wird die operative Reibung von KeePass real. Credential-Rotation erfordert das Neuschlüsseln der gesamten Datenbank. Offboarding bedeutet, dass alle ihr Masterpasswort ändern. Die Zugriffssteuerung ist binär — entweder hat jemand das Masterpasswort oder nicht. Passwork eliminiert diese Reibung: granulare Berechtigungen, automatisiertes Offboarding, Audit-Trails pro Benutzer und Echtzeit-Sync ohne Konflikte.
Wenn Ihre Organisation unter Compliance-Anforderungen operiert (GDPR, SOC 2, NIS2, ISO 27001, PCI DSS), wird die Lücke noch größer. Eine gemeinsam genutzte KeePass-Datenbank besteht kein Audit. Passwork mit RBAC, Audit-Logging, AD-Integration und Zero-Knowledge-Verschlüsselung erfüllt Compliance-Anforderungen ohne administrativen Overhead.
Fazit

KeePass ist ein Ausgangspunkt. Für einen Solo-Admin oder ein Zwei-Personen-Team ohne externe Audit-Anforderungen erfüllt es seinen Zweck. Für jedes Team, das über diese Schwelle hinaus operiert, erzeugt es mehr Risiko, als es eliminiert.
Die administrative Schuld akkumuliert sich leise: Sync-Konflikte, die hier eine Stunde kosten, eine Offboarding-Rotation, die dort einen Tag kostet, ein Audit-Finding, das ein Quartal kostet. Nichts davon erscheint auf der KeePass-Rechnung, weil es keine gibt. Aber die Kosten sind real.
Der nächste Schritt ist unkompliziert: Kartieren Sie Ihr aktuelles Credential-Inventar, identifizieren Sie, welche Teams Zugriff auf welche Systeme teilen, und bewerten Sie, ob Ihr aktuelles Tool Ihnen sagen kann, wer auf was Zugriff hat. Wenn es das nicht kann, haben Sie Ihre Antwort.

Wenn Ihr Team über KeePass hinausgewachsen ist, wurde Passwork genau für diesen Moment entwickelt. Sie erhalten granulare Berechtigungen, Echtzeit-Sync, Audit-Logs pro Benutzer, AD-Integration, MFA-Durchsetzung und Zero-Knowledge-Verschlüsselung. Alles ohne die operative Schuld der Verwaltung gemeinsamer Masterpasswörter und manueller Credential-Rotation. Passwork kostenlos testen
Häufig gestellte Fragen

Ist KeePass sicher für die Unternehmensnutzung?
KeePass verwendet AES-256-Verschlüsselung und ist Open-Source mit einer langen Sicherheitsbilanz, was es kryptographisch solide macht. Für die Unternehmensnutzung liegt das Sicherheitsrisiko im Fehlen von Audit-Logs, granularen Zugriffssteuerungen und MFA-Durchsetzung. Diese Lücken erzeugen Compliance-Risiko unter GDPR Artikel 32 und SOC 2 CC6.1.
Können mehrere Benutzer eine KeePass-Datenbank teilen?
Ja, aber mit erheblichen Einschränkungen. KeePass hat keine Echtzeit-Sync-Engine. Wenn zwei Benutzer dieselbe .kdbx-Datei gleichzeitig auf einem Netzlaufwerk bearbeiten, überschreibt das letzte Speichern das vorherige ohne Merge oder Warnung. Die eigene Dokumentation von KeePass beschreibt dies als bekannte Einschränkung, die manuelle Workarounds erfordert.
Was ist der Hauptunterschied zwischen KeePass und einem Unternehmens-Passwortmanager?
Der Kernunterschied liegt in der Zugriffsarchitektur. KeePass verwendet ein einziges Masterpasswort, das von allen Benutzern geteilt wird — es gibt keine individuellen Konten, keine Berechtigungen pro Benutzer und keine Aktivitätslogs. Ein Unternehmens-Passwortmanager weist jedem Benutzer seine eigene authentifizierte Sitzung zu, erzwingt rollenbasierten Zugriff auf bestimmte Tresore und protokolliert jede Credential-Interaktion.
Unterstützt KeePass Active Directory oder LDAP?
Nein. KeePass hat keine native AD- oder LDAP-Integration. Benutzer-Provisioning und -Deprovisioning sind vollständig manuell. Im Gegensatz dazu integrieren sich Enterprise-Grade-Credential-Manager mit AD/LDAP, sodass Zugriffsrechte automatisch der Verzeichnisgruppen-Mitgliedschaft folgen.
Warum besteht KeePass Compliance-Audits nicht?
KeePass kann keine Nachweise darüber erbringen, wer wann auf welche Zugangsdaten zugegriffen hat. SOC 2 Type II-Auditoren verlangen Zugriffs-Logs unter CC6.1. GDPR Artikel 32 verlangt nachweisbare Zugriffssteuerungen. Eine .kdbx-Datei mit einem gemeinsamen Masterpasswort erfüllt keine der beiden Anforderungen, unabhängig davon, wie stark die Verschlüsselung ist.
Wann sollte ein KMU von KeePass zu einem Unternehmens-Passwortmanager wechseln?
Die praktische Schwelle liegt bei fünf oder mehr Benutzern, jeglicher Compliance-Verpflichtung (SOC 2, GDPR, HIPAA, ISO 27001) oder jeder Situation, in der der Zugriffsverlauf nachgewiesen werden muss. Wenn beim Ausscheiden eines Mitarbeiters Zugangsdaten rotiert werden müssen, anstatt ein Benutzerkonto zu widerrufen, ist das ein klares Signal, dass das aktuelle Tool nicht zweckgeeignet ist.