Die meisten Organisationen haben Jahre damit verbracht, ihre Perimeter zu härten — Firewalls, Endpoint-Erkennung, Threat-Intelligence-Feeds. Dennoch bleibt der häufigste Weg, über den Bedrohungsakteure eindringen, unverändert: Sie melden sich einfach an.
Phishing rangierte 2025 als häufigster initialer Angriffsvektor und war für 16 % aller Datenschutzverletzungen verantwortlich — gegenüber dem zweiten Platz im Vorjahr — laut IBMs Cost of a Data Breach Report 2025. Kompromittierte Anmeldedaten fielen auf den dritten Platz, gehörten aber weiterhin zu den kostspieligsten Vektoren mit durchschnittlich 4,67 Mio. USD pro Vorfall. Sicherheitsverletzungen, bei denen gestohlene Daten über mehrere Umgebungen verteilt waren, waren mit durchschnittlich 5,05 Mio. USD pro Vorfall am teuersten — ein Beleg für die erhöhte Komplexität von Angriffen auf hybride Infrastrukturen.
Hier liegt das Paradoxon: Je mehr eine Organisation in Infrastruktur investiert, desto mehr Anmeldedaten erzeugt sie. B2B-Organisationen betreiben Hunderte von Cloud-Anwendungen, On-Premise-Systemen und eine wachsende Schicht nicht-menschlicher Identitäten: Servicekonten, API-Integrationen, KI-Agenten. Jede davon trägt Anmeldedaten. Die meisten dieser Anmeldedaten werden inkonsistent oder gar nicht verwaltet. Selbst das kleinste Leck gibt Angreifern die Möglichkeit, alle privaten Daten zu erlangen.
Enterprise-Passwortmanagement adressiert dies direkt: zentralisierte Speicherung, automatisierte Richtliniendurchsetzung und der Audit-Trail, den Compliance-Teams benötigen. Im Gegensatz zu Consumer-Passwortmanagern, die für den individuellen Gebrauch konzipiert sind, bieten Enterprise-Passwortmanagement-Lösungen rollenbasierte Zugriffskontrollen (RBAC), administrative Überwachung und Integration mit bestehender Sicherheitsinfrastruktur.
Dieser Leitfaden gibt IT-Direktoren, Sicherheitsarchitekten und CISOs ein praktisches Framework zur Bewertung von Deployment-Modellen, zum Verständnis der Sicherheitsarchitektur, zur Durchführung eines phasenweisen Rollouts und zur Erstellung eines fundierten Business Case.
Enterprise-Passwortmanagement verstehen
Verschlüsselte Dateien bildeten einst die Grundlage der organisatorischen Speicherung von Anmeldedaten. Im Laufe der Zeit entstanden dedizierte Plattformen zur Automatisierung der Rotation, Durchsetzung von Komplexitätsregeln und Überwachung auf Sicherheitsverletzungen. Heute integrieren sich diese Systeme direkt in die Identity-Management-Infrastruktur und verwalten vollständige Anmeldedaten-Lebenszyklen — von der Bereitstellung bis zur Dekommissionierung.
Organisationen fallen typischerweise in eine von drei Kategorien basierend auf ihrem Ansatz:
- Basis: Tabellenkalkulationen oder freigegebene Dokumente, keine zentrale Überwachung, keine Richtliniendurchsetzung.
- Mittel: Dedizierte Tools mit verschlüsselten Tresoren und eingeschränkter Freigabe — aber die IT kann Richtlinien immer noch nicht automatisch durchsetzen.
- Enterprise: Richtlinienbasierte Systeme, die alle Anmeldedaten zentralisieren. Automatisierte Rotation läuft nach Zeitplan, rollenbasierte Berechtigungen spiegeln die Organisationsstruktur wider, und vollständige Audit-Trails erfüllen Compliance-Anforderungen.
Was ist Enterprise-Passwortmanagement?
Im Kern ist Enterprise-Passwortmanagement ein verschlüsselter Tresor, der Passwörter, API-Schlüssel, Zertifikate und andere Geheimnisse unter strengen Zugriffskontrollen speichert. Berechtigungssysteme bestimmen Abrufrechte basierend auf Benutzerrollen und Kontext. Richtlinienautomatisierung setzt Komplexitätsregeln und Rotationspläne konsistent durch, während Nutzungslimits unbefugtes Verhalten verhindern. Jede Interaktion erstellt einen Protokolleintrag, der sowohl Sicherheitsüberprüfungen als auch Compliance-Berichte unterstützt.
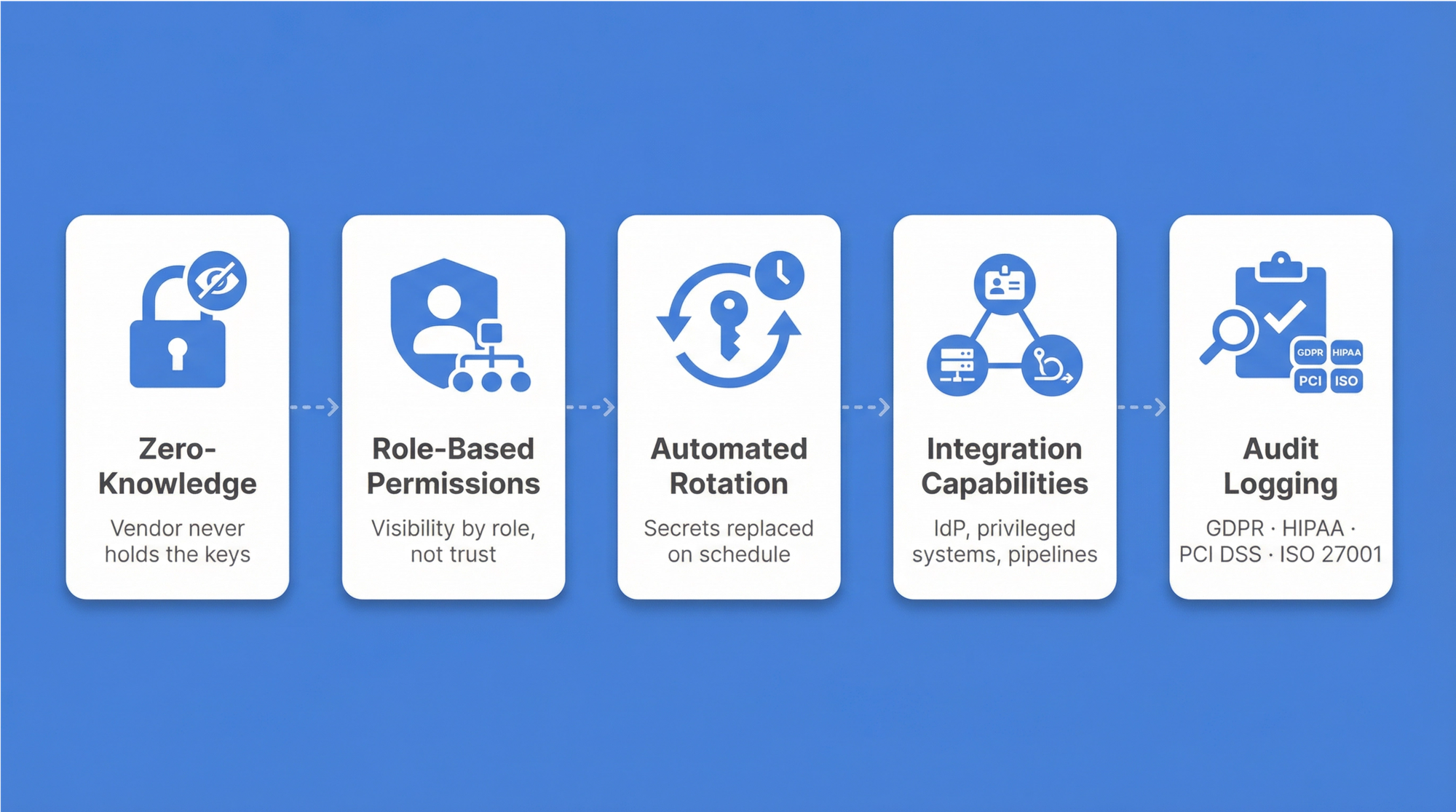
Fünf architektonische Prinzipien definieren eine reife Implementierung:
- Zero-Knowledge-Architektur — nur autorisierte Benutzer können ihre Daten entschlüsseln; der Anbieter hält niemals die Schlüssel.
- Rollenbasierte Berechtigungen — die Sichtbarkeit wird basierend auf organisatorischen Rollen eingeschränkt, nicht auf individuellem Vertrauen.
- Automatisierte Rotation — Geheimnisse werden nach definierten Zeitplänen ersetzt, um den Schaden bei einem Leak zu begrenzen.
- Integrationsfähigkeiten — Verbindungen erstrecken sich über Identity-Provider, privilegierte Systeme und Deployment-Pipelines.
- Compliance-fähige Audit-Protokollierung — jedes Zugriffsereignis auf Anmeldedaten wird mit Zeitstempel, Benutzeridentität und Kontext aufgezeichnet und erzeugt den Nachweispfad, den GDPR-, HIPAA-, PCI-DSS- und ISO-27001-Audits erfordern.
Für C-Level-Führungskräfte steht die Compliance-Dokumentation typischerweise ganz oben auf der Prioritätenliste — Regulierungsbehörden verlangen vollständige Audit-Trails und dokumentierte Kontrollen. Über den regulatorischen Druck hinaus folgt Risikominderung, wenn Passwort-Wiederverwendung eliminiert und starke Sicherheitsstandards etabliert werden. Die betriebliche Effizienz verbessert sich messbar, wenn passwortbezogene Support-Tickets zurückgehen.
Wesentliche Unterschiede zwischen Consumer- und Enterprise-Passwortmanagern
Consumer-Passwortmanager dienen einzelnen Benutzern, die persönliche Anmeldedaten speichern. Enterprise-Lösungen erfüllen organisatorische Anforderungen mit zentralisierter Verwaltung, Richtliniendurchsetzung und Compliance-Funktionen, für die Consumer-Tools nie konzipiert wurden.
| Funktion | Consumer-Lösungen | Enterprise-Lösungen |
|---|---|---|
| Administration | Nur individuelle Kontrolle | Zentralisierte IT-Überwachung mit rollenbasierter Delegation |
| Zugriffskontrollen | Einfaches Teilen zwischen Benutzern | Rollenbasierte Zugriffskontrolle, die die Organisationsstruktur widerspiegelt |
| Audit-Funktionen | Eingeschränkte persönliche Nutzungsprotokolle | Vollständige Zugriffsprotokolle für Compliance und Sicherheitsüberwachung |
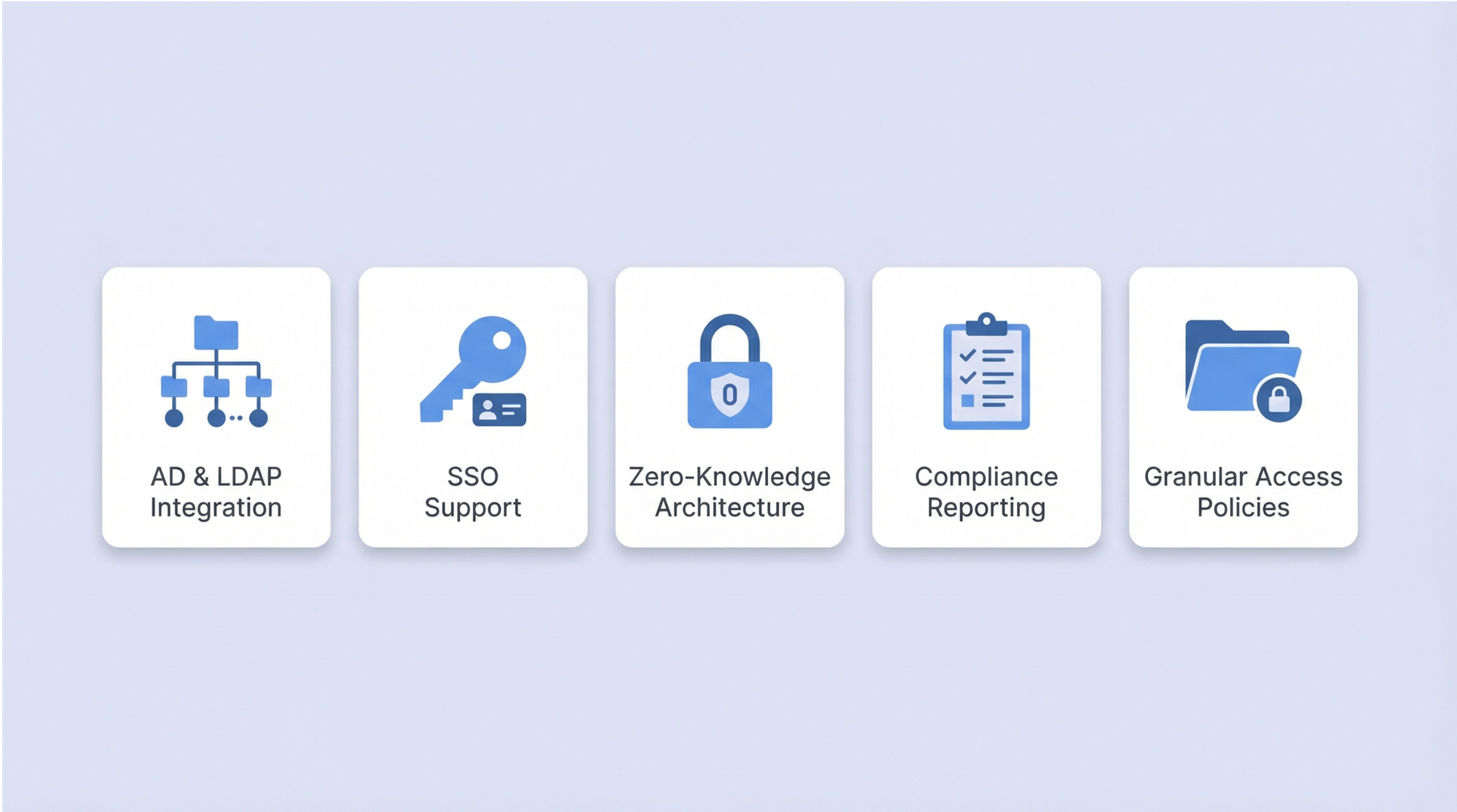
| Integration | Browser-Erweiterungen, mobile Apps | Identity-Provider (AD — Active Directory; LDAP — Lightweight Directory Access Protocol; SSO — Single Sign-On), PAM-Systeme, Deployment-Pipelines |
| Deployment | Nur Cloud-Abonnement | On-Premise-, Cloud- oder Hybrid-Optionen |
| Secrets-Management | Nur Passwort-Fokus | Passwörter plus API-Schlüssel, Zertifikate, Servicekonten |
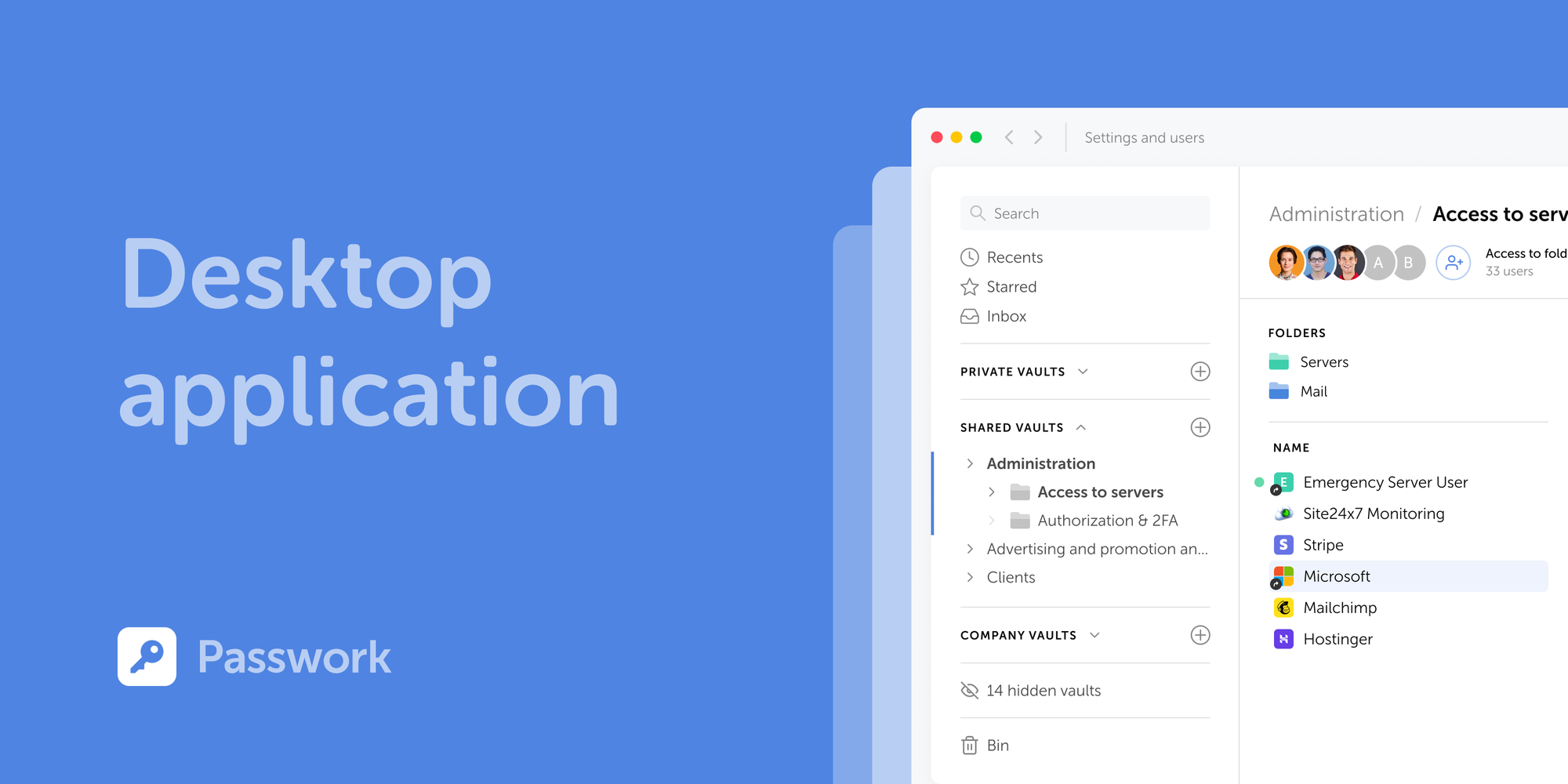
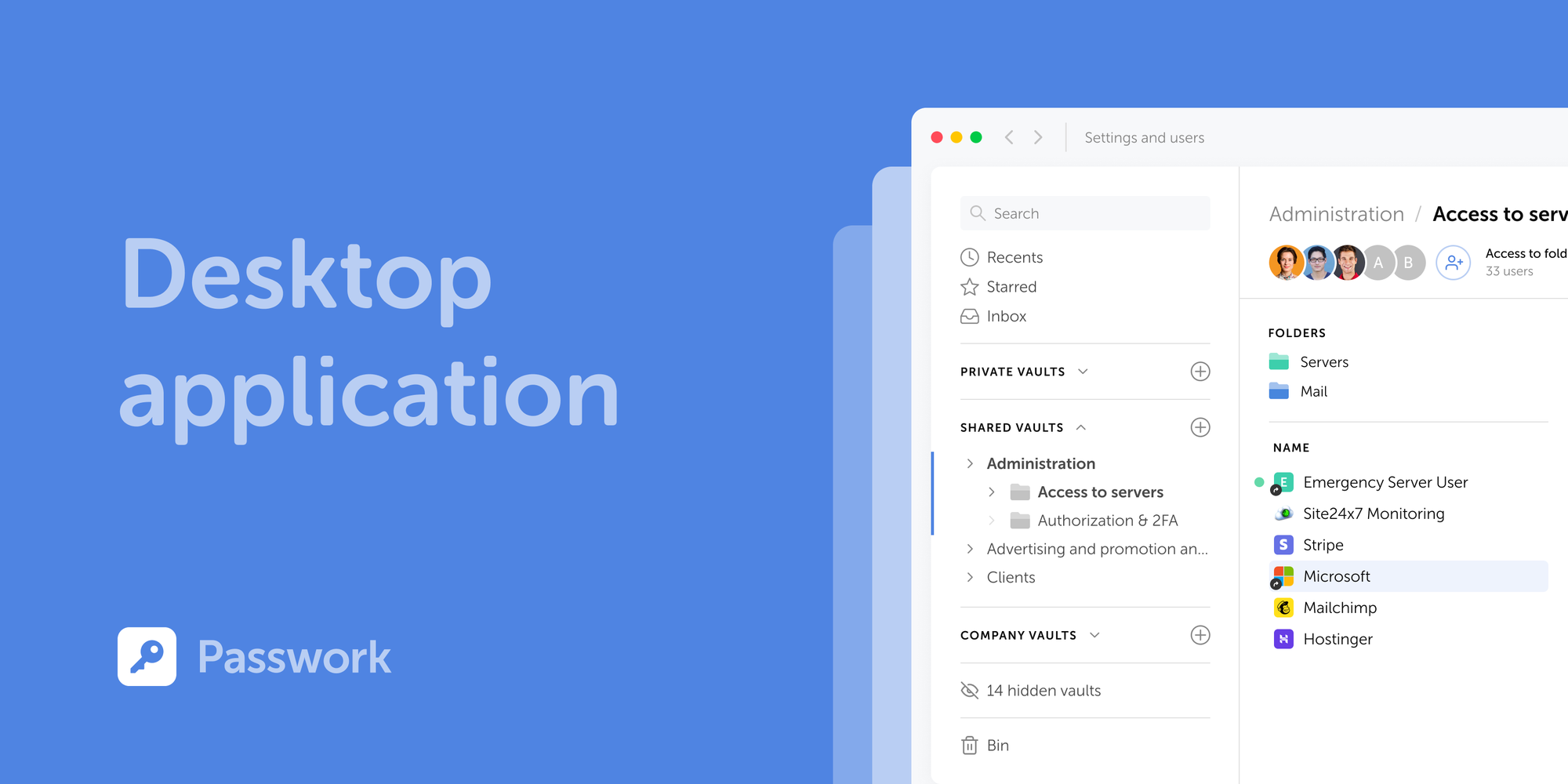
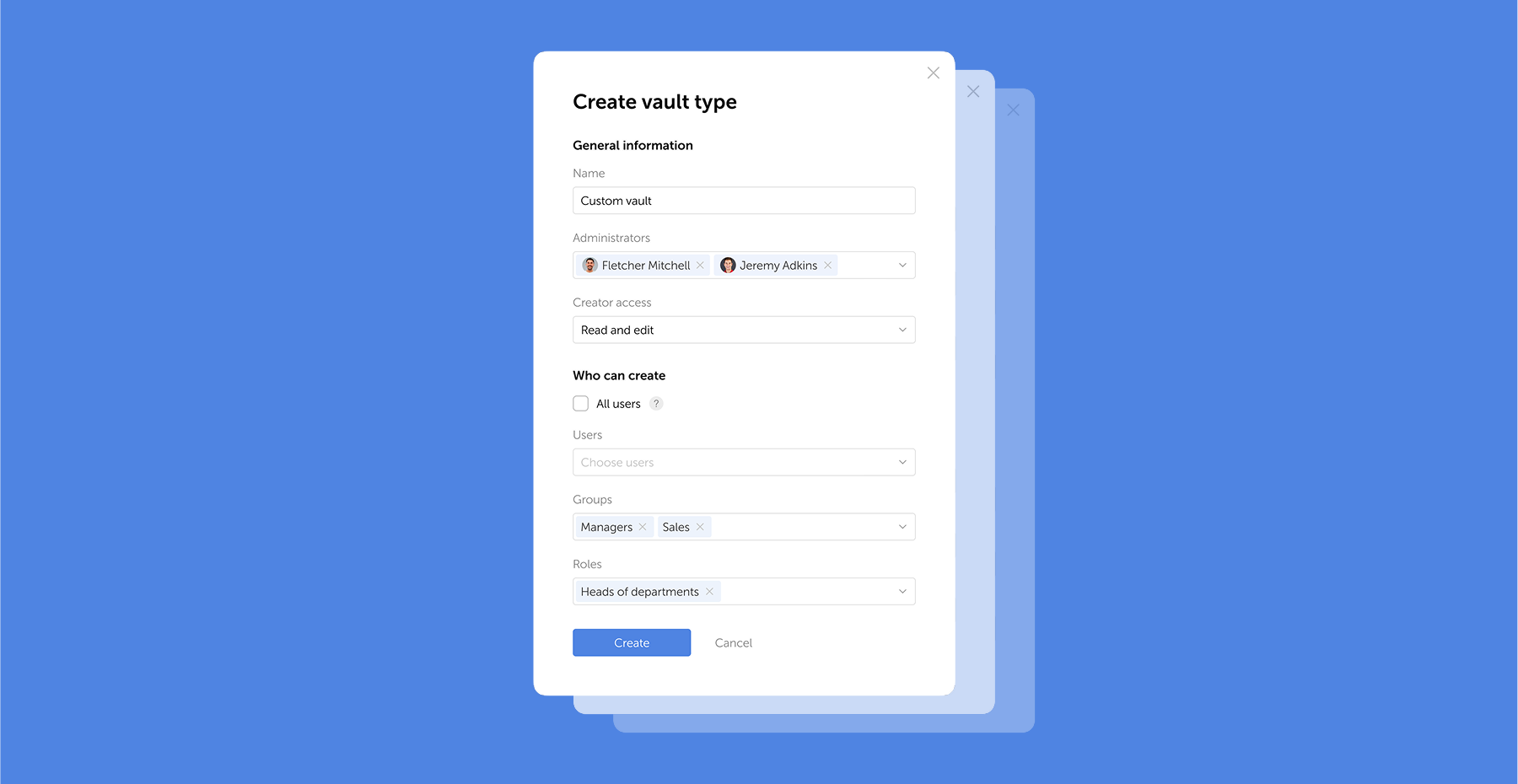
Passwork ist mit diesen Enterprise-Anforderungen als Standard konzipiert: rollenbasierte Zugriffskontrolle, die Teamstrukturen widerspiegelt, erweiterte administrative Tools für IT-Überwachung, On-Premise-Deployment für Datensouveränität, AD/LDAP/SSO-Integrationen mit bestehender Identitätsinfrastruktur und detaillierte Audit-Funktionen für Compliance-Berichte.
Kritische Komponenten eines Enterprise-Passwort-Tresors
Enterprise-Tresore setzen mehrere Schutztechnologien über den gesamten Lebenszyklus der Anmeldedaten ein. Zero-Knowledge-Verschlüsselung stellt sicher, dass nur autorisierte Benutzer sensible Daten entschlüsseln können — selbst Systemadministratoren können nicht auf gespeicherte Passwörter zugreifen. Das Prinzip der minimalen Rechtevergabe (PoLP) regelt jede Berechtigungsentscheidung. Automatisierte Rotation verkürzt Expositionsfenster, wenn Anmeldedaten entweichen.
- Zero-Knowledge-Architektur implementiert clientseitige Verschlüsselung: Die Entschlüsselung erfolgt auf Benutzergeräten, niemals auf Servern. Dies ist die architektonische Garantie, die vertrauenswürdige Enterprise-Lösungen von denen unterscheidet, die nur Sicherheit behaupten.
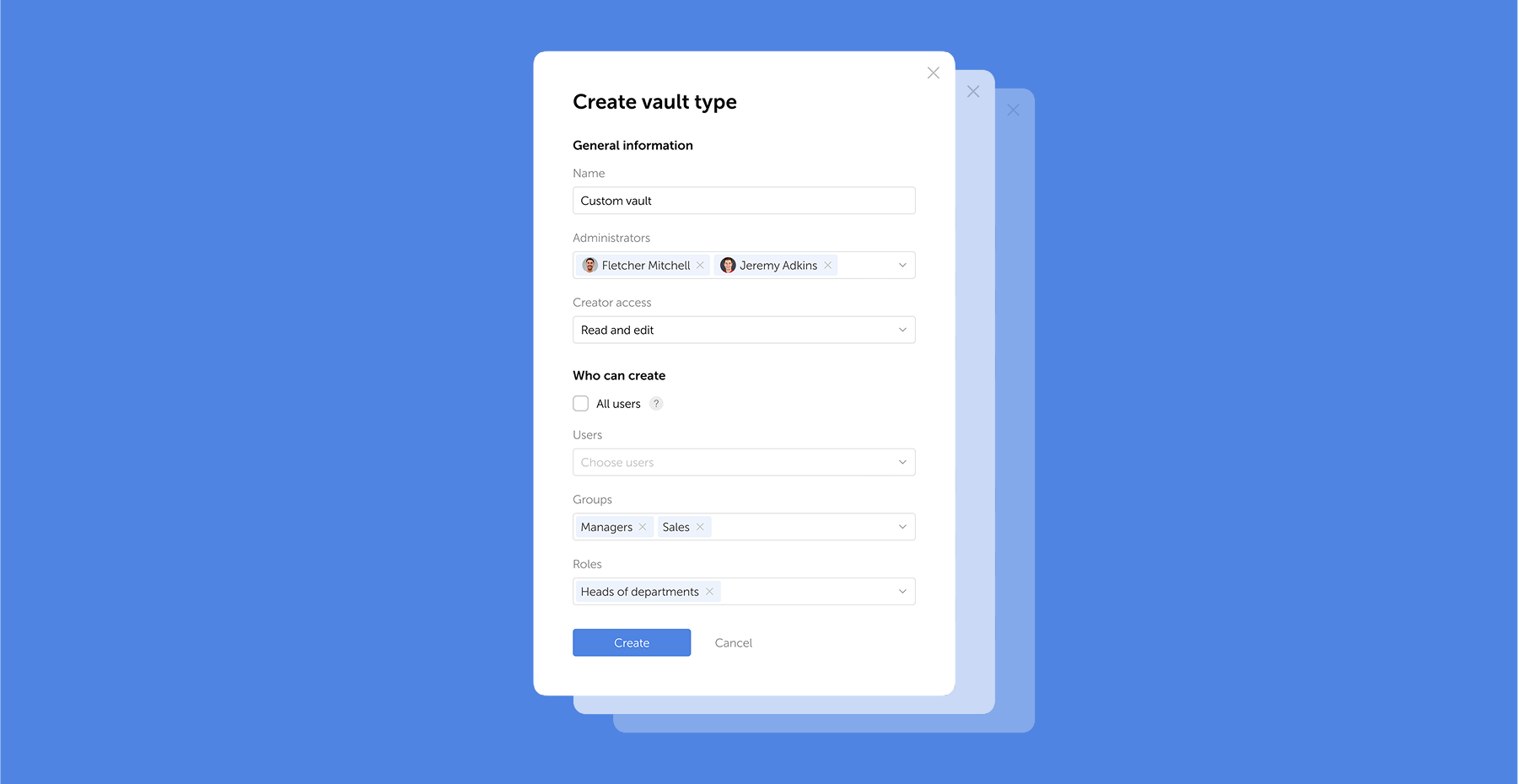
- Rollenbasierte Zugriffskontrolle bildet Organisationsstrukturen auf Berechtigungsmodelle ab. IT-Administratoren sehen Infrastruktur-Anmeldedaten; Finanzteams greifen auf Buchhaltungssystem-Passwörter zu. Für spezifische Aufgaben bietet Just-in-Time-Abruf von Anmeldedaten temporären Zugriff, der nach der Nutzung automatisch abläuft — betriebliche Flexibilität ohne dauerhafte Exposition.
Privileged-Access-Management-Integration
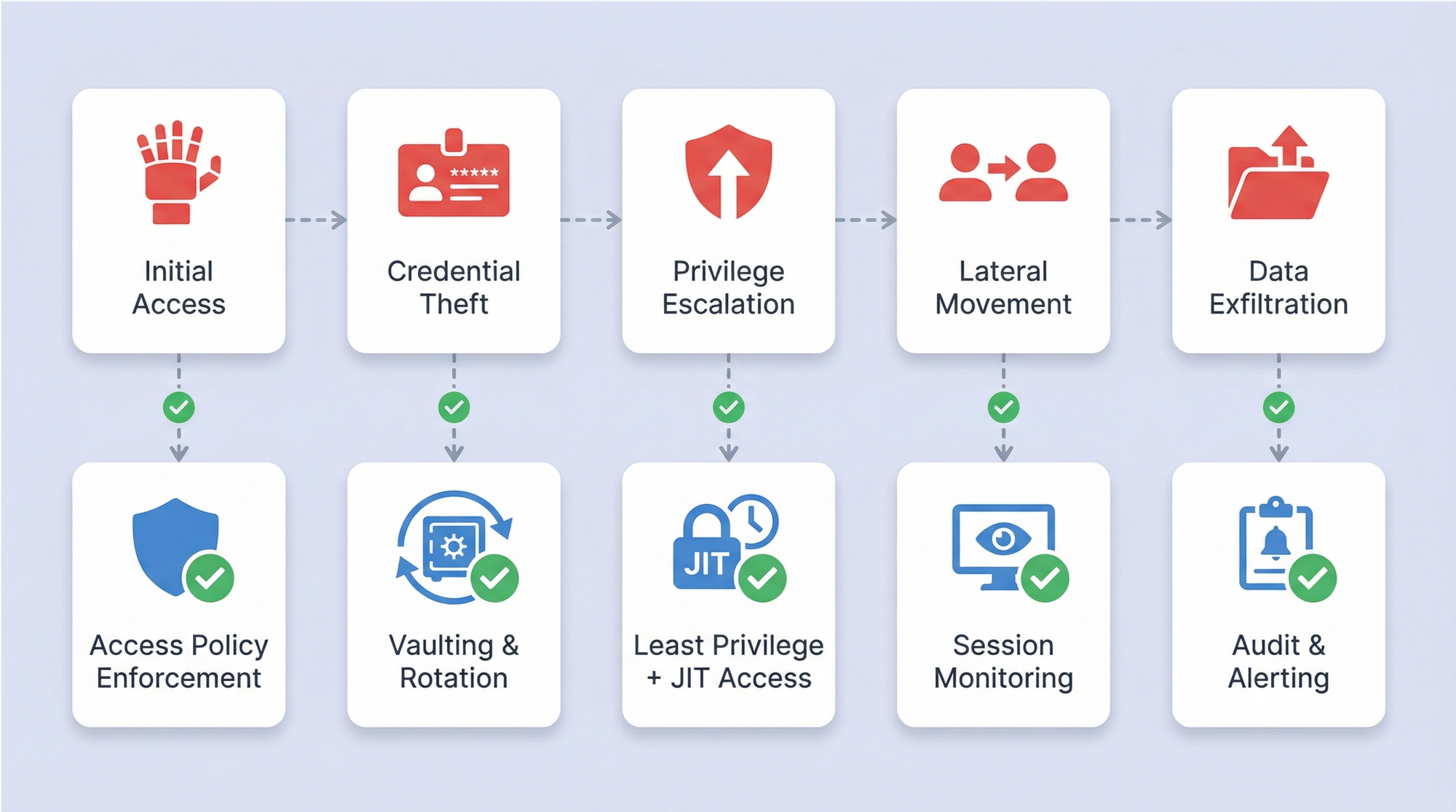
Privileged Access Management kontrolliert administrative Anmeldedaten, die erhöhten Systemzugriff gewähren — Domain-Administratoren, Datenbank-Superuser, Cloud-Administratoren. Ihre Kompromittierung gibt Angreifern die vollständige Kontrolle über kritische Infrastruktur.
PAM-Integration adressiert dies durch mehrere Schichten: Automatisierte Erkennung lokalisiert privilegierte Konten in der gesamten Infrastruktur, Echtzeit-Überwachung erfasst administrative Aktivitäten in Echtzeit, und Genehmigungsworkflows leiten Anfragen für hohe Privilegien an zuständige Manager weiter, bevor Zugriff gewährt wird. Verschlüsselte Speicherung in Kombination mit geplanter Rotation hält diese Anmeldedaten während ihres gesamten Lebenszyklus geschützt.
Verwaltung nicht-menschlicher Anmeldedaten
Automatisierte Systeme benötigen Authentifizierungsmechanismen, die ohne menschliches Eingreifen funktionieren: Servicekonten, API-Schlüssel, Anwendungspasswörter. Deployment-Pipelines verbinden sich mit Produktionsservern; Überwachungstools fragen kontinuierlich Datenbankmetriken ab. In den meisten Unternehmen übersteigt die Anzahl nicht-menschlicher Anmeldedaten die traditionellen Benutzerpasswörter bei weitem.
Diese Anmeldedaten stellen eine spezifische Verwaltungsherausforderung dar. Servicekonten überleben oft die Projekte, die sie erstellt haben. Das Ändern eines API-Schlüssels erfordert die Aktualisierung jedes Systems, das ihn referenziert. Ohne aktive Governance sammeln sich verwaiste Anmeldedaten an, während Teams die Rotation vermeiden, um Produktions-Deployments nicht zu unterbrechen.
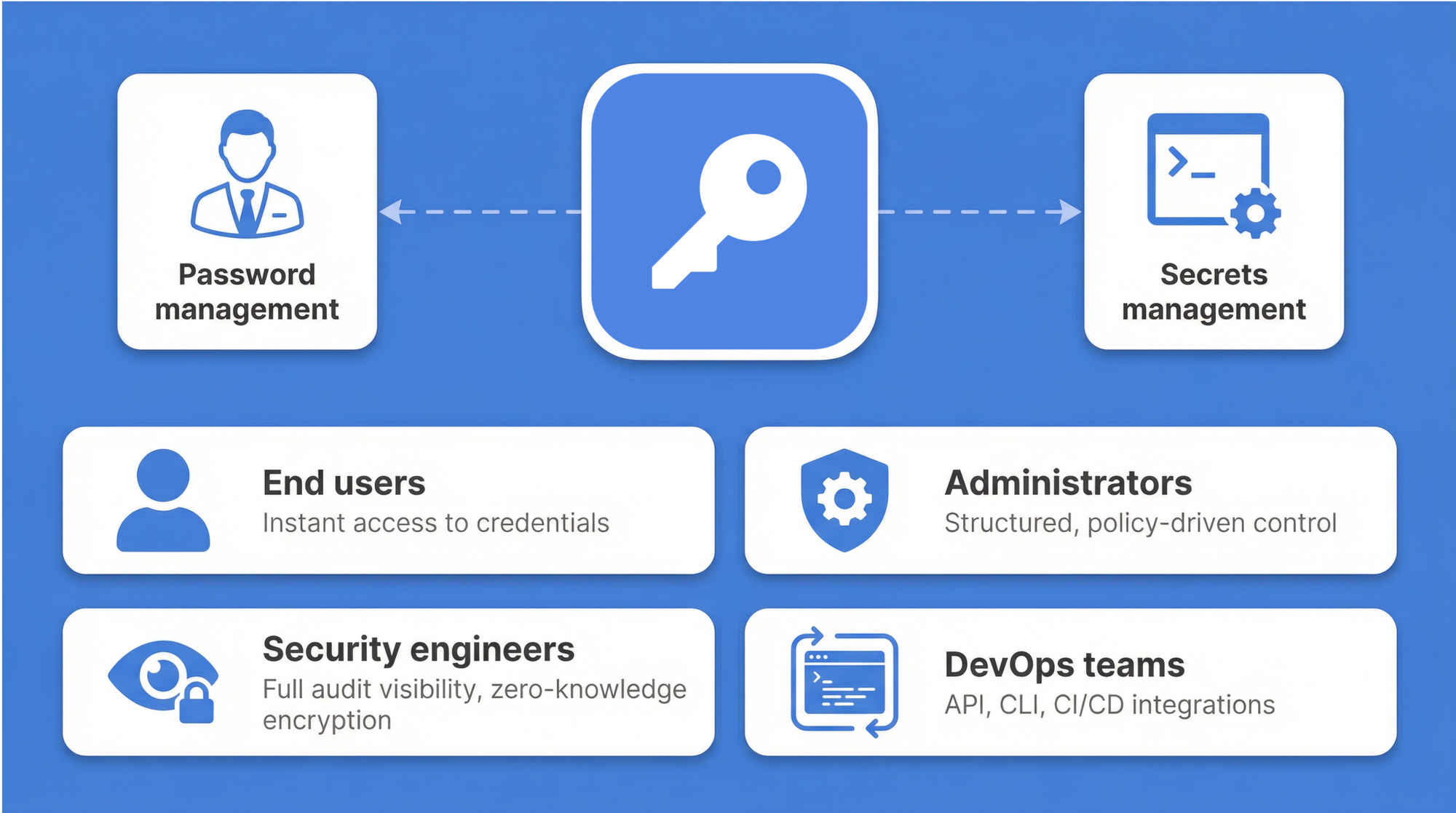
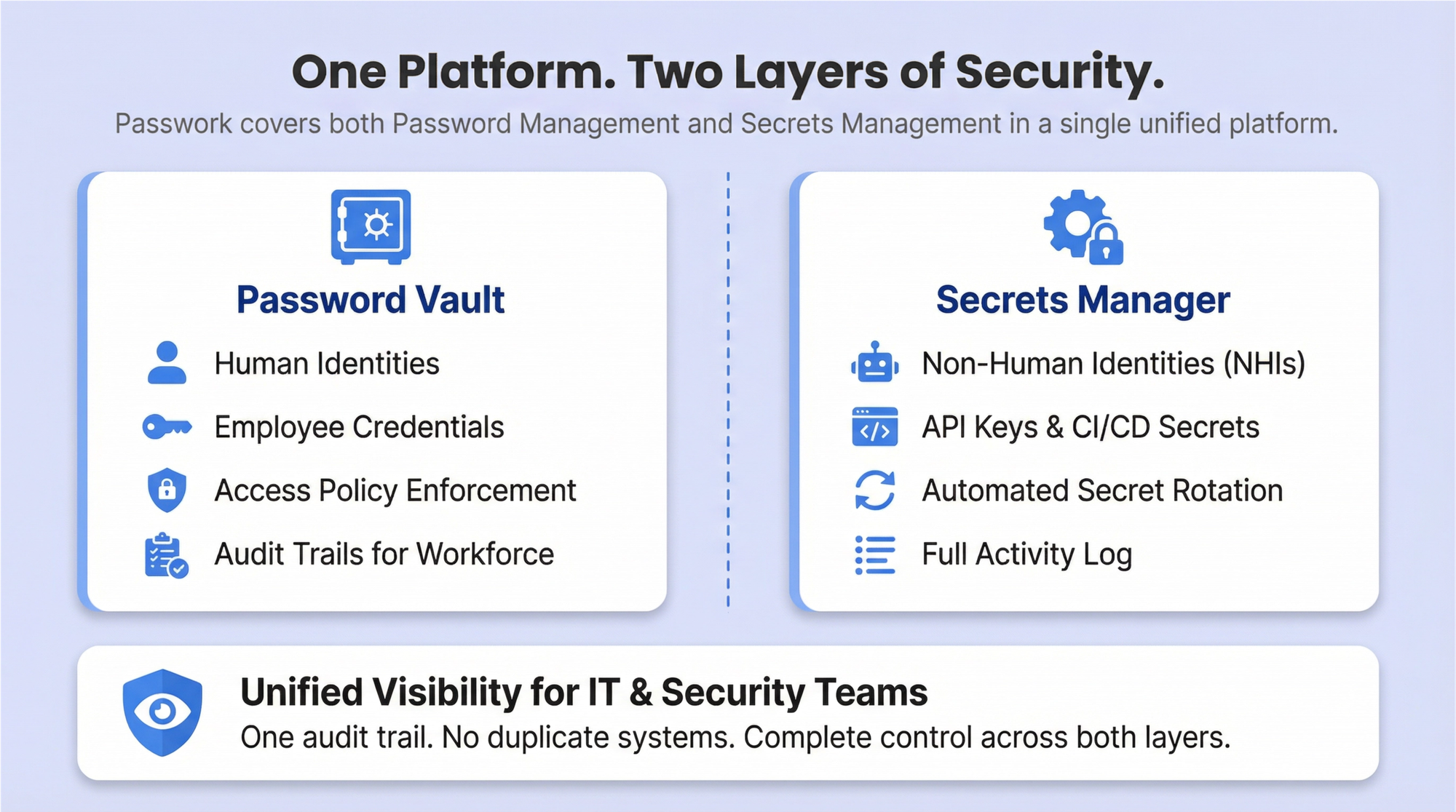
Passwork adressiert dies direkt. Während die meisten Enterprise-Passwortmanager nur menschliche Anmeldedaten verarbeiten, vereint Passwork Passwortmanagement mit DevOps-Secrets-Management in einer einzigen Plattform. Deployment-Pipelines integrieren sich direkt mit API-Schlüssel-Rotation; Lebenszyklus-Tracking verfolgt Servicekonten von der Erstellung bis zur Dekommissionierung. Die gemeinsame Unterbringung von menschlichen und nicht-menschlichen Anmeldedaten eliminiert doppelte Tools und die damit verbundene betriebliche Komplexität.
Erkennung und Verwaltung von Anmeldedaten
Vergessene Servicekonten, Schatten-IT-Passwörter und aufgegebene Auftragnehmer-Anmeldedaten bleiben in der gesamten Infrastruktur verborgen, bis etwas schiefgeht. Automatisierte Scans durchsuchen Netzwerke, Server, Anwendungen und Cloud-Plattformen, um diese nicht verwalteten Geheimnisse zu lokalisieren. Das Ergebnis ist ein vollständiges Inventar der Anmeldedaten — oft werden Hunderte von unbekannten Konten aufgedeckt, die eine ausnutzbare Angriffsfläche schaffen.
Hochrisiko-Befunde erhalten sofortige Aufmerksamkeit: privilegierte Konten ohne Rotationspläne, Passwörter, die teamübergreifend geteilt werden, Servicekonten ohne designierten Besitzer. Lebenszyklus-Management bringt diese unter zentralisierte Governance und etabliert klare Besitzverhältnisse zusammen mit Rotationsrichtlinien und Audit-Tracking. GDPR und PCI DSS verlangen von Organisationen, genau zu dokumentieren, wo sensible Daten existieren und wer Zugriffsberechtigungen hat. Automatisierte Erkennung macht dieses regulatorische Mandat erreichbar statt nur ambitioniert.
Erweiterte Sicherheitsfunktionen
Enterprise-Passwortmanagement kombiniert mehrere Sicherheitstechnologien zum Schutz von Anmeldedaten. AES-256-Verschlüsselung mit Zero-Knowledge-Architektur bedeutet, dass alle Verschlüsselung clientseitig erfolgt: Passwörter werden auf Benutzergeräten verschlüsselt, bevor sie an Server übertragen werden, und nur Benutzer mit den richtigen Entschlüsselungsschlüsseln können auf Klartext-Passwörter zugreifen.
Das Open Web Application Security Project (OWASP) bestätigt, dass aktuelle Hashing-Algorithmen — einschließlich Argon2id, bcrypt und PBKDF2 — eingebaute Salting-Mechanismen enthalten, die keine zusätzlichen Konfigurationsschritte erfordern.
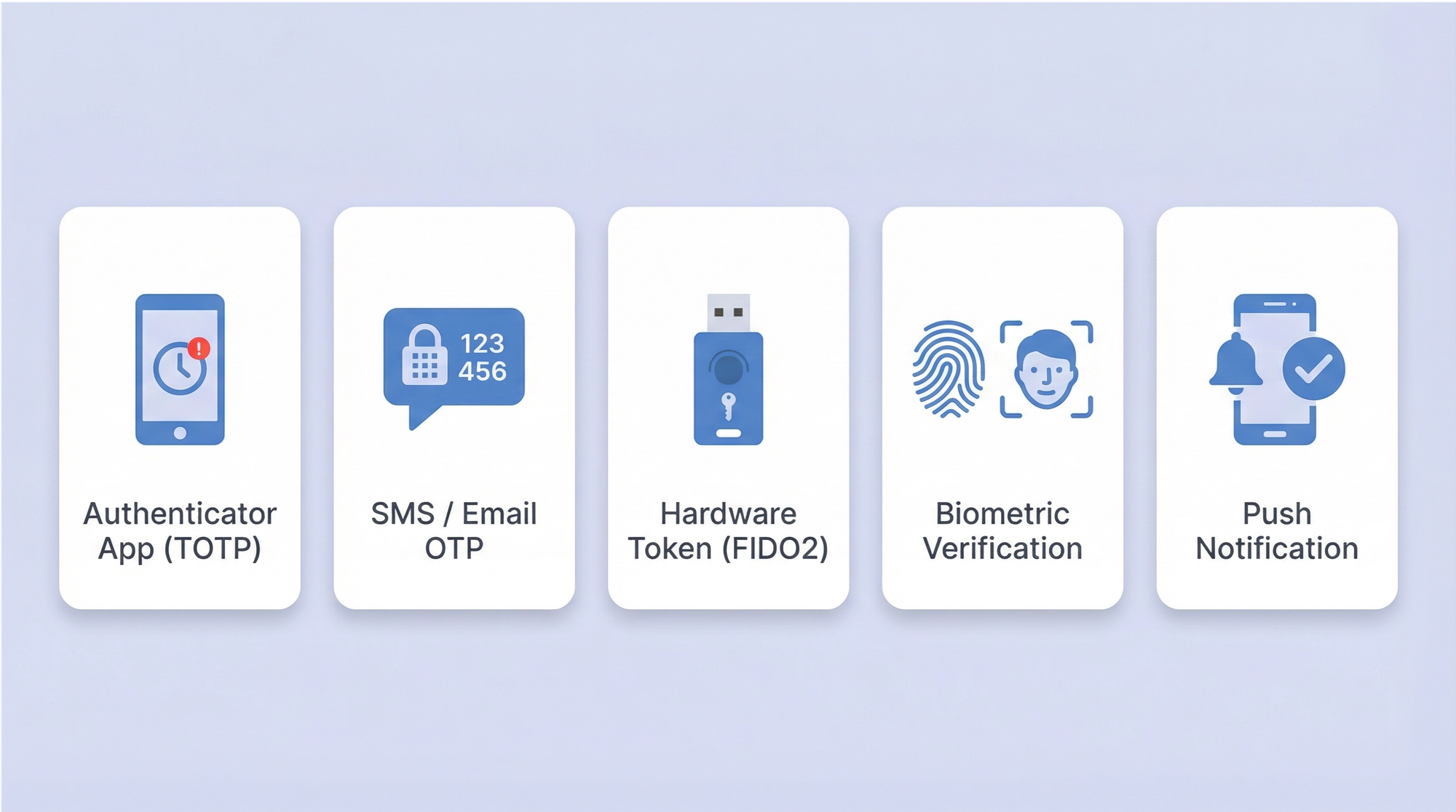
Über Passwörter und Verschlüsselung hinaus fügt Multi-Faktor-Authentifizierung Verifizierungsschichten hinzu. Zeitbasierte Einmalpasswörter (TOTP) generieren sechsstellige Codes, die alle 30 Sekunden aktualisiert werden. Für Phishing-resistente Hardware-Authentifizierung sind FIDO2/WebAuthn-Sicherheitsschlüssel die stärkere Option — der Schlüssel kann physisch nicht auf einer gefälschten Domain verwendet werden. Organisationen können diese Methoden stapeln: Passwort plus TOTP für Standardzugriff, Passwort plus FIDO2-Schlüssel für privilegierte Konten.
Enterprise-Passwort-Tresore stützen sich auf mehrere Sicherheitstechnologien, die zusammenarbeiten. Verschlüsselung schützt gespeicherte Daten, MFA fügt Verifizierungsschichten hinzu, und automatisierte Überwachung erkennt Bedrohungen, bevor Schaden entsteht.
| Sicherheitsfunktion | Technologie | Schutzniveau | Implementierung |
|---|---|---|---|
| Zero-Knowledge-Verschlüsselung | AES-256 mit clientseitigen Schlüsseln | Höchstes — Anbieter kann nicht entschlüsseln | Schlüssel verlassen niemals Benutzergeräte, Entschlüsselung erfolgt lokal |
| Multi-Faktor-Authentifizierung | TOTP, Hardware-Schlüssel, Biometrie | Stark — erfordert mehrere Nachweise | Integration mit bestehender Infrastruktur, stapelbare Methoden |
| Automatisierte Rotation | Geplanter Ersatz von Anmeldedaten | Reduziert Expositionsfenster | Integration mit Systemen, richtliniengesteuerte Zeitpläne |
| Audit-Protokollierung | Vollständige Zugriffsverfolgung | Detektiv — identifiziert verdächtige Muster | Unveränderliche Aufzeichnungen, Compliance-Berichte |
Vergleich von Enterprise-Passwortmanagement-Lösungen
Die Plattformauswahl hängt von Deployment-Flexibilität, Integrationsanforderungen und organisatorischer Größe ab. Regulatorisches Umfeld, Teamstruktur und technische Kapazität prägen alle die Entscheidung.
Open-Source-Optionen bieten Code-Transparenz mit aktiven Communities. Reine Cloud-Plattformen tauschen Deployment-Flexibilität gegen Komfort und schnellere Ersteinrichtung. Passwork adressiert eine Lücke, die andere offen lassen: die Kombination von Passwortmanagement mit DevOps-Secrets-Management bei gleichzeitiger Unterstützung von On-Premise- und Cloud-Deployment.
Für Organisationen mit 50–200 Benutzern sind Kosteneffizienz und Verwaltungseinfachheit am wichtigsten — IT-Manager benötigen On-Premise-Optionen für regulatorische Kontrolle ohne Enterprise-Grade-Komplexität. Organisationen mit 200–1.000 Benutzern haben andere Prioritäten: Compliance-Berichte, zentralisierte Governance und Integration mit bestehender Identitätsinfrastruktur. Regulierte Branchen — Gesundheitswesen, Finanzen, Regierung — bewegen sich konsequent in Richtung On-Premise-Deployment, wo lokale Datensouveränitätsgesetze dies erfordern.
Leitfaden für B2B-Organisationen: Wie Sie ihn lesen
Die folgenden Abschnitte sind als Entscheidungsrahmen strukturiert. Jeder Abschnitt ist in sich geschlossen. Organisationen, die sich bereits für ein Deployment-Modell entschieden haben, können direkt zur Implementierung springen.
Teil 1: Deployment-Modelle — Cloud, On-Premise oder Hybrid?
Die Deployment-Entscheidung prägt alles, was folgt: Datenresidenz, Wartungsaufwand, Kostenstruktur und Integrationskomplexität. Es gibt keine universell richtige Antwort — nur die richtige Passung für das regulatorische Umfeld und die betriebliche Kapazität einer bestimmten Organisation.
Schnellvergleich
| Funktion | Cloud-gehostet | On-Premise | Hybrid |
|---|---|---|---|
| Kontrolle | Vom Anbieter verwaltete Infrastruktur | Volle Kontrolle über Daten und Infrastruktur | On-Premise für sensible Daten, Cloud für Flexibilität |
| Compliance | Stark; Anbieter verfügen typischerweise über SOC 2, ISO 27001 Zertifizierungen | Ideal für strenge Datenresidenz-Anforderungen | Konfigurierbar zur Erfüllung spezifischer regionaler Anforderungen |
| Kostenmodell | Abonnementbasiert (OpEx) | Höhere Vorabinvestition (CapEx) | Mischung aus CapEx und OpEx |
| Wartung | Vom Anbieter übernommen | Erfordert dedizierte IT-Ressourcen | Geteilte Verantwortung |
| Skalierbarkeit | Hoch | Begrenzt durch interne Infrastruktur | Hoch |
Cloud-Deployment
Cloud-gehostete Lösungen bieten die schnellste Time-to-Value. Anbieter übernehmen Infrastruktur, Updates und Verfügbarkeit. Für verteilte Belegschaften mit begrenzter interner IT-Kapazität beseitigt dieses Modell betriebliche Reibung. Der Kompromiss ist die Abhängigkeit von der Sicherheitslage des Anbieters und, für regulierte Branchen, potenzielle Spannungen mit Datenresidenz-Gesetzen.
On-Premise-Deployment
On-Premise-Installation hält alle Anmeldedaten innerhalb der eigenen Infrastruktur der Organisation. Für Gesundheitswesen, Finanzdienstleistungen und Regierungssektoren — wo GDPR, HIPAA oder nationale Datensouveränitätsgesetze gelten — ist dies oft der einzig gangbare Weg. Das Kostenprofil unterscheidet sich: höhere Vorab-Infrastrukturinvestition, aber keine wiederkehrenden Pro-Benutzer-Gebühren, die sich bei Skalierung summieren. Für Organisationen mit 200 oder mehr Benutzern begünstigt die langfristige Wirtschaftlichkeit häufig On-Premise.
Hybrid-Deployment
Die meisten großen Unternehmen passen nicht eindeutig in eine der Kategorien. Ein multinationaler Konzern, der in der EU, den USA und APAC tätig ist, steht in jeder Region vor unterschiedlichen regulatorischen Anforderungen. Ein Finanzinstitut benötigt möglicherweise On-Premise-Speicherung für privilegierte Anmeldedaten, während es Cloud-basierten Zugriff für allgemeine Belegschaftskonten ermöglicht.
Das Hybrid-Modell handhabt dies direkt: Sensible Anmeldedaten und privilegierte Konten bleiben On-Premise unter voller organisatorischer Kontrolle, während die breitere Belegschaft eine Cloud-verbundene Oberfläche nutzt. Diese Architektur unterstützt auch schrittweise Migration — Organisationen können Workloads inkrementell verschieben, anstatt sich zu einem vollständigen Cutover zu verpflichten.
Für Unternehmen, die über mehrere Umgebungen oder Geschäftseinheiten hinweg bereitstellen, bietet Passwork Mengenrabatte bei Multi-Instanz-Käufen — was das Hybrid-Modell kosteneffektiv im großen Maßstab macht, nicht nur architektonisch sinnvoll. Testen Sie Passwork kostenlos, um den vollständigen Funktionsumfang zu evaluieren, bevor Sie sich für ein Deployment-Modell entscheiden.
Teil 2: Sicherheitsarchitektur — über den Tresor hinaus
Verschlüsselung im Ruhezustand ist Standardvoraussetzung. Die Sicherheitsarchitektur eines ausgereiften Enterprise-Passwortmanagers geht erheblich weiter.
Zero-Knowledge-Architektur
Zero-Knowledge-Architektur bedeutet, dass der Anbieter niemals die Schlüssel zur Entschlüsselung von Kundendaten besitzt. Alle Ver- und Entschlüsselung erfolgt clientseitig auf dem Gerät des Benutzers. Selbst wenn die Infrastruktur des Anbieters kompromittiert würde, würde der Angreifer nur Chiffretext abrufen. Passwork dokumentiert seinen Verschlüsselungsalgorithmus offen in seiner Technischen Dokumentation — Sicherheitsteams können die Implementierung unabhängig verifizieren, anstatt Anbieterbehauptungen einfach zu akzeptieren.
Authentifizierungsschichten
- Multi-Faktor-Authentifizierung: TOTP fügt eine zweite Verifizierungsschicht für Standardzugriff hinzu. WebAuthn-Hardware-Sicherheitsschlüssel bieten Phishing-resistente Authentifizierung für privilegierte Konten — der Schlüssel kann physisch nicht gegen eine gefälschte Domain authentifizieren. Organisationen können diese Methoden basierend auf Sensibilitätsstufe stapeln.
- Single Sign-On: Integration mit bestehenden Identity-Providern — Microsoft Entra ID, Okta oder LDAP-basierten Verzeichnissen — bedeutet, dass Benutzer sich über Infrastruktur authentifizieren, der sie bereits vertrauen. Wenn ein Mitarbeiter das Unternehmen verlässt, entzieht die Deprovisionierung über den Identity-Provider sofort den Tresor-Zugriff.
- Passkeys: Passkeys ersetzen das Passwort vollständig für unterstützte Anwendungen. Der private Schlüssel verlässt niemals das Gerät des Benutzers; die Authentifizierung verwendet eine kryptographische Challenge-Response. Mit der zunehmenden Unterstützung von Passkeys durch Enterprise-Anwendungen wird dies der praktische Weg zur Eliminierung von Passwörtern für menschliche Benutzer.
Teil 3: Implementierung und Rollout — ein phasenweiser Ansatz mit Passwork
Die Technologieauswahl ist der einfache Teil. Die schwierigere Arbeit ist organisatorischer Natur: Migration bestehender Anmeldedaten, Konfiguration von Integrationen und Tausende von Mitarbeitern dazu zu bringen, ihre Handhabung von Passwörtern zu ändern. Ein phasenweiser Rollout reduziert Risiken und baut in jeder Phase Vertrauen auf, bevor der Umfang erweitert wird.
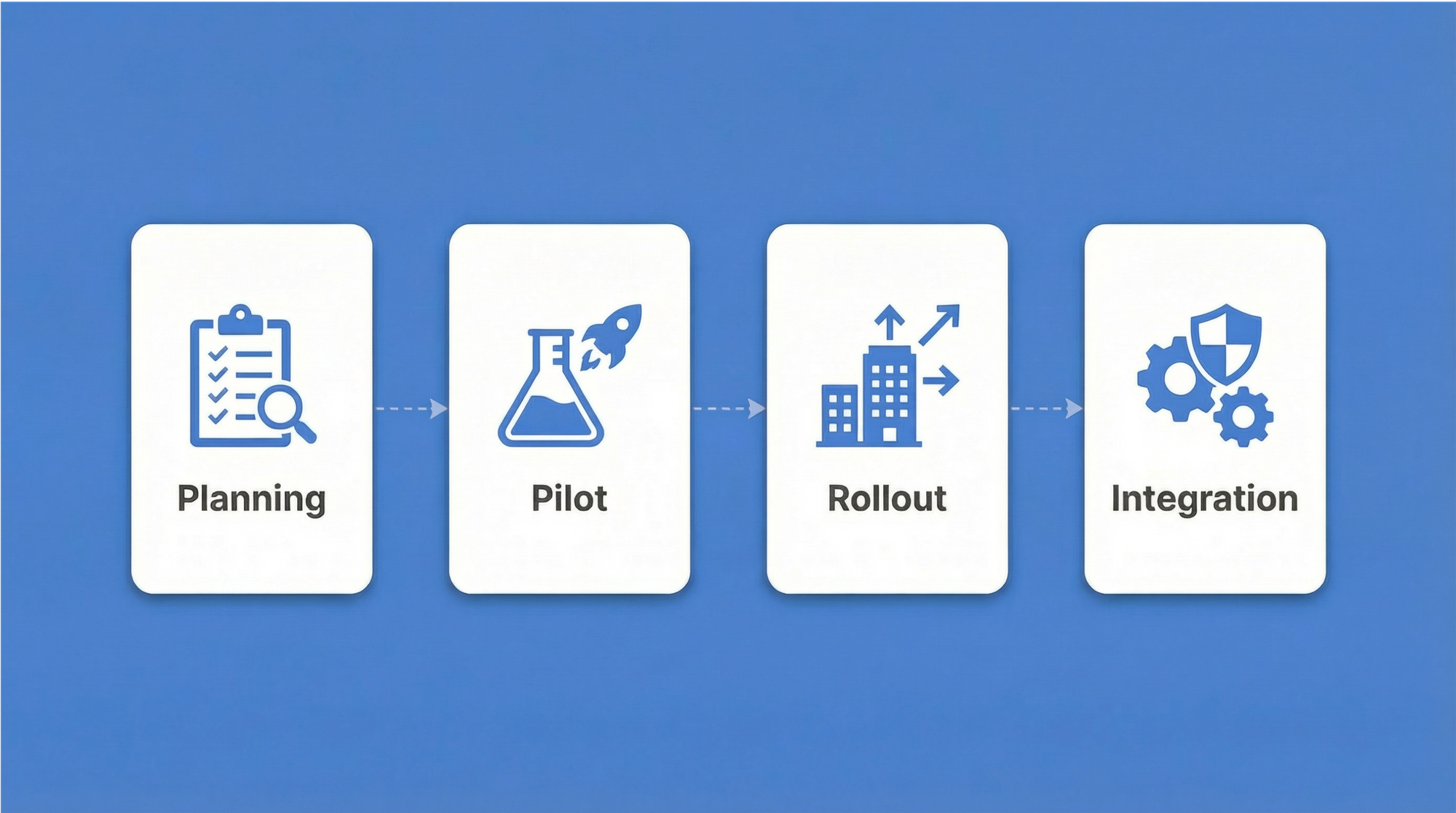
Phase 1: Planung und Anbieterauswahl
Bevor Software installiert wird, benötigt das Projektteam ein klares Bild dessen, was es verwaltet. Diese Phase umfasst:
- Inventar der Anmeldedaten: Katalogisierung bestehender Passwörter, Servicekonten, API-Schlüssel und Zertifikate. Die meisten Organisationen entdecken deutlich mehr Anmeldedaten als erwartet — einschließlich verwaister Konten von ehemaligen Mitarbeitern und vergessener Servicekonten von stillgelegten Projekten.
- Compliance-Mapping: Dokumentation, welche regulatorischen Rahmenwerke gelten (GDPR, HIPAA, PCI DSS, ISO 27001) und welche Audit-Nachweise jeweils erforderlich sind.
- Deployment-Modell-Entscheidung: Basierend auf Datenresidenz-Anforderungen und IT-Kapazität wird On-Premise, Cloud oder Hybrid ausgewählt.
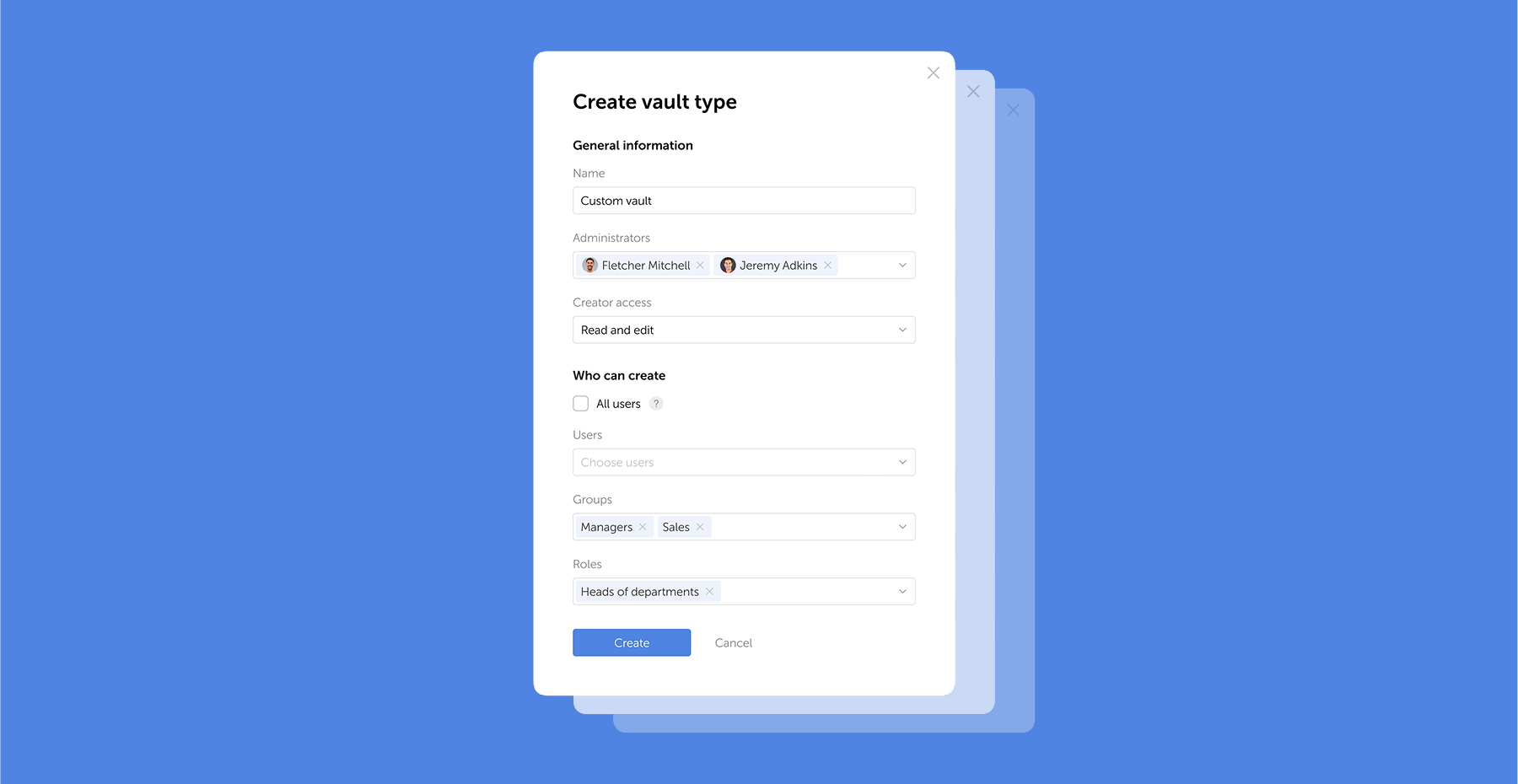
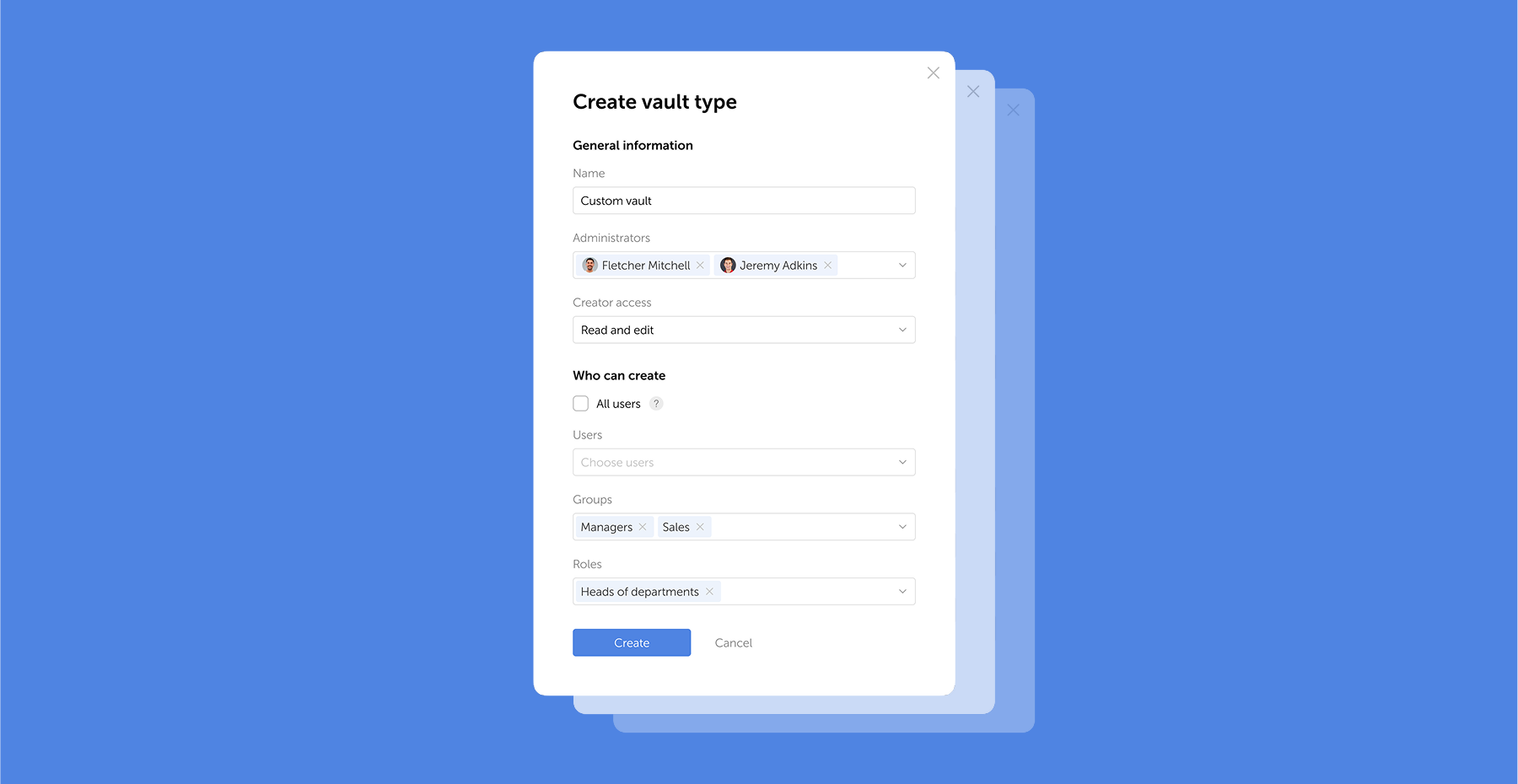
- Rollenstruktur-Design: Entwurf des initialen Berechtigungsmodells — wie Passworks rollenbasierte Zugriffskontrolle die Organisationshierarchie widerspiegeln wird.
- Evaluation der Anbieter-Shortlist: Bewertung von Integrationsanforderungen (Active Directory, LDAP, SSO-Provider), Secrets-Management-Bedürfnissen und Gesamtbetriebskosten.
Phase 2: Pilotprogramm
Die IT-Abteilung führt den Piloten durch. Diese Gruppe hat den technischen Kontext, um Integrationsprobleme zu identifizieren, und die Toleranz für Unvollkommenheiten, die Endbenutzer nicht haben.
Während dieser Phase:
- Identity-Provider-Integration wird konfiguriert — Verbindung von Passwork mit Active Directory oder LDAP für Benutzerbereitstellung und Aktivierung von SSO über den bestehenden Identity-Provider der Organisation.
- Passwortrichtlinien gehen live: Komplexitätsanforderungen, Rotationspläne und MFA-Durchsetzung.
- Migration der Anmeldedaten beginnt inkrementell. Passwork unterstützt Import aus gängigen Formaten und bietet Migrationsunterstützung für Organisationen, die von Legacy-Plattformen wechseln.
- Pilotteilnehmer geben strukturiertes Feedback zu Benutzerfreundlichkeit, Browser-Erweiterungs-Verhalten und Workflow-Auswirkungen.
Migration von einem Legacy-Passwortmanager
Organisationen, die von Legacy-Passwortmanagern wechseln, stehen vor einer spezifischen Herausforderung: Benutzer haben jahrelang gespeicherte Anmeldedaten in einem bestehenden System, und ein harter Cutover verursacht Störungen. Passworks Migrations-Tools unterstützen phasenweisen Import: Anmeldedaten werden in Batches nach Abteilung oder Anmeldedatentyp verschoben, was Parallelbetrieb während des Übergangszeitraums ermöglicht. Das Legacy-System bleibt im Nur-Lese-Modus verfügbar, bis die Migration als abgeschlossen verifiziert ist.
Phase 3: Abteilungsweiser Rollout und Change Management
Die Expansion erfolgt Abteilung für Abteilung, nicht auf einmal. Finanzen, HR und Betrieb haben jeweils unterschiedliche Anmeldedaten-Sets und unterschiedliche technische Komfortniveaus. Sequentielles Onboarding ermöglicht es dem IT-Team, Probleme in einer Abteilung zu adressieren, bevor zur nächsten übergegangen wird.
Change Management ist der Punkt, an dem die meisten Enterprise-Rollouts erfolgreich sind oder scheitern. Häufige Widerstandsmuster und wie sie adressiert werden können:
| Einwand | Antwort |
|---|---|
| „Ich benutze bereits den eingebauten Passwortmanager meines Browsers" | Browser-Passwortmanagern fehlt zentralisierte Admin-Kontrolle, Audit-Protokollierung und MFA-Durchsetzung. Sie verarbeiten auch keine Servicekonten oder API-Schlüssel. |
| „Das fügt Reibung zu meinem Workflow hinzu" | Passworks Browser-Erweiterung übernimmt Autofill automatisch. Nach der ersten Woche berichten die meisten Benutzer von schnellerer Authentifizierung, nicht langsamerer. |
| „Was passiert, wenn das System ausfällt?" | On-Premise-Deployment eliminiert die Abhängigkeit von der Anbieterverfügbarkeit. Offline-Zugriffsmodi sind für kritische Anmeldedaten verfügbar. |
| „Ich vertraue einem Dritten unsere Passwörter nicht an" | Zero-Knowledge-Architektur bedeutet, dass Passwork niemals Entschlüsselungsschlüssel besitzt. Der Anbieter kann gespeicherte Anmeldedaten nicht lesen, selbst wenn er dazu gezwungen wird. |
Während dieser Phase migrieren auch Servicekonten und Anwendungs-Anmeldedaten in das System.
Phase 4: Integration, Automatisierung und Governance
Die letzte Phase vervollständigt die Integrationsschicht und etabliert laufende Governance.
- Verzeichnissynchronisierung: SCIM-Bereitstellung automatisiert das Benutzerlebenszyklus-Management. Wenn die HR-Abteilung einen neuen Mitarbeiter im Identity-Provider anlegt, erstellt Passwork automatisch dessen Konto mit den korrekten Rollenzuweisungen. Wenn jemand das Unternehmen verlässt, erfolgt die Deprovisionierung sofort — keine manuellen Schritte, kein verwaister Zugriff.
- Automatisierte Rotation: Geplante Rotation der Anmeldedaten läuft ohne menschliches Eingreifen. Passwork integriert sich mit Deployment-Pipelines, sodass die Rotation eines API-Schlüssels gleichzeitig jedes abhängige System aktualisiert — wodurch das Problem „Wir können das nicht rotieren, weil etwas kaputtgehen würde" eliminiert wird.
- Compliance-Berichte: Automatisierte Audit-Berichte generieren Nachweise für GDPR-, HIPAA-, PCI-DSS- und ISO-27001-Audits. Das Audit-Log erfasst jedes Zugriffsereignis auf Anmeldedaten mit Zeitstempel, Benutzeridentität und Kontext.
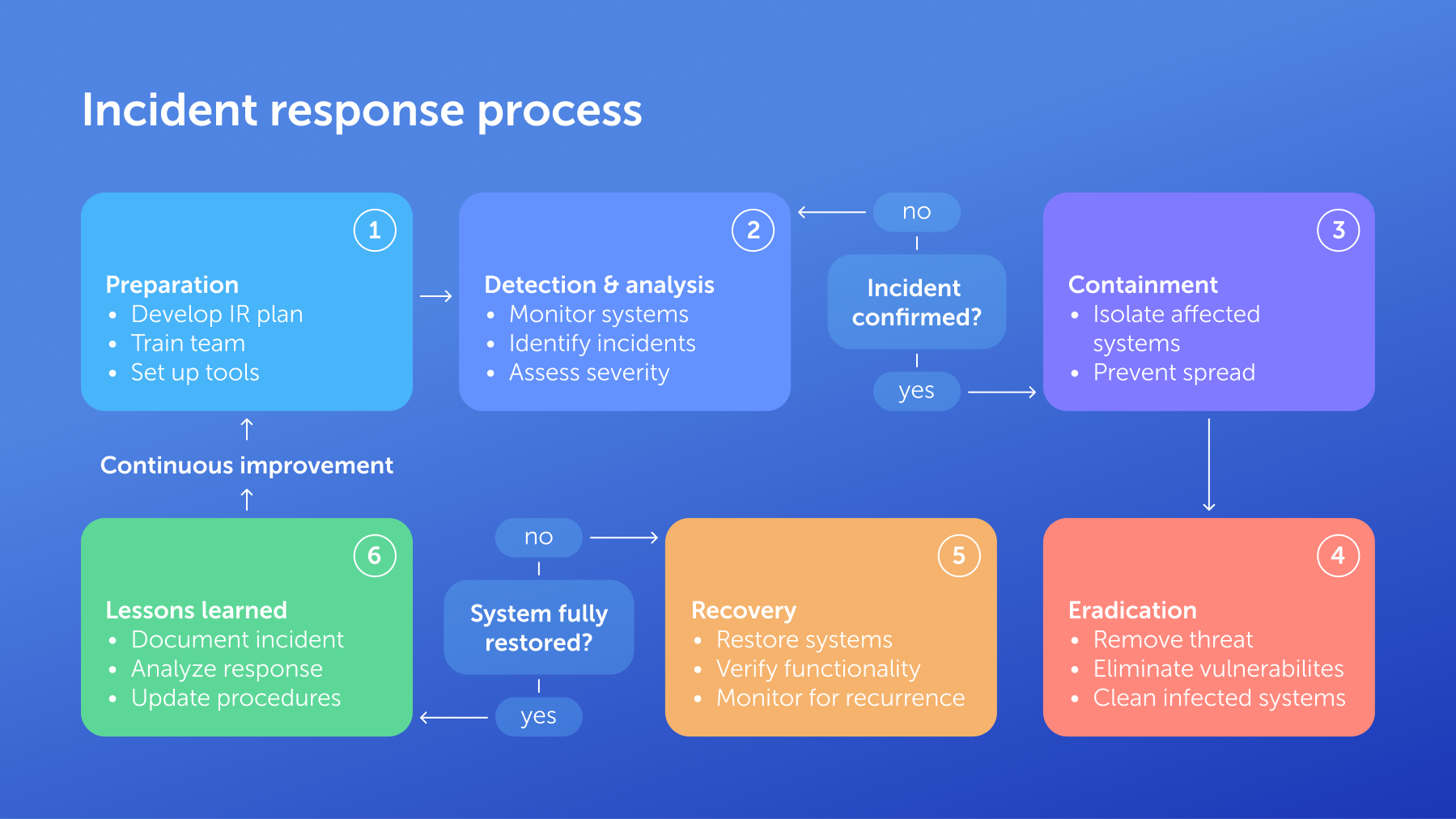
- Laufende Governance: Das Projektteam etabliert Überprüfungsrhythmen — vierteljährliche Zugriffsüberprüfungen, jährliche Richtlinien-Updates und Incident-Response-Verfahren, die Workflows zur Widerrufung von Anmeldedaten einschließen.
Teil 4: Der Business Case — ROI berechnen
Sicherheitsinvestitionen erfordern finanzielle Begründung. Die Daten hier sind eindeutig.
Reduzierung der Help-Desk-Kosten
Passwortbezogene Probleme machen laut Gartner-Forschung 20–50 % aller IT-Help-Desk-Anrufe aus. Ein einzelnes Passwort-Reset verursacht überraschend hohe Vollkosten, wenn IT-Arbeit einbezogen wird — und bei Skalierung über Hunderte oder Tausende von Mitarbeitern summieren sich diese Tickets zu einem erheblichen und vollständig vermeidbaren Betriebsaufwand.
Self-Service-Passwort-Reset kombiniert mit einem Enterprise-Passwort-Tresor, der Autofill und Credential-Injection übernimmt, eliminiert die Mehrheit dieser Tickets. Benutzer, die niemals ein Passwort manuell eingeben oder sich merken müssen, erzeugen weit weniger Sperrungsereignisse.
Vermeidung von Breach-Kosten
Die globalen durchschnittlichen Kosten einer Datenschutzverletzung erreichten 2025 4,44 Millionen USD, gegenüber 4,88 Millionen USD im Jahr 2024 — aber Verletzungen, bei denen Daten über mehrere Umgebungen verteilt waren, betrugen durchschnittlich 5,05 Millionen USD. Eine einzelne Kompromittierung von Anmeldedaten, die laterale Bewegung über Cloud- und On-Premise-Systeme ermöglicht, kann diese Zahl leicht überschreiten, sobald Regulierungsstrafen, Rechtskosten und Reputationsschäden einbezogen werden.
Enterprise-Passwortmanagement reduziert die Breach-Wahrscheinlichkeit durch mehrere Mechanismen: Eliminierung der Passwort-Wiederverwendung, automatische Durchsetzung von Komplexität, Erkennung kompromittierter Anmeldedaten durch Breach-Monitoring und Reduzierung von Expositionsfenstern durch automatisierte Rotation.
Teil 5: Die Zukunft der Authentifizierung — Verwaltung nicht-menschlicher Identitäten
Menschliche Anmeldedaten sind der sichtbare Teil des Problems. Der weniger sichtbare Teil wächst schneller.
Der Aufstieg nicht-menschlicher Identitäten
Servicekonten, API-Schlüssel, Datenbank-Verbindungsstrings, OAuth-Tokens und TLS-Zertifikate übersteigen in den meisten Enterprise-Umgebungen mittlerweile die Anzahl menschlicher Benutzerpasswörter. KI-Agenten — autonome Systeme, die sich bei APIs, Datenbanken und internen Tools authentifizieren, um Aufgaben zu erledigen — beschleunigen diesen Trend. Jeder Agent trägt seine eigenen Anmeldedaten. Jede Anmeldedaten-Information ist eine potenzielle Angriffsfläche.
Im Gegensatz zu menschlichen Passwörtern sind nicht-menschliche Anmeldedaten oft langlebig, werden selten rotiert und gehören niemandem bestimmten. Der Entwickler, der vor drei Jahren ein Servicekonto erstellt hat, hat das Unternehmen möglicherweise verlassen. Der in einem Deployment-Skript eingebettete API-Schlüssel wird möglicherweise von einem Dutzend nachgelagerter Systeme referenziert. Seine Änderung erfordert teamübergreifende Koordination — also wird er nicht geändert.
Secrets-Management als Disziplin
Die Verwaltung nicht-menschlicher Anmeldedaten erfordert einen dedizierten Ansatz — was die Branche Secrets-Management nennt. Passwork vereint Passwortmanagement und Secrets-Management in einer einzigen Plattform. Deployment-Pipelines integrieren sich direkt mit API-Schlüssel-Rotation; Servicekonto-Lebenszyklus-Tracking läuft parallel zur Governance menschlicher Anmeldedaten. Organisationen eliminieren die betriebliche Komplexität des Betriebs separater Tools für menschliche und nicht-menschliche Anmeldedaten.
Das passwortlose Unternehmen
Die Entwicklung ist klar: Passwörter werden ersetzt, nicht verbessert. Passkeys eliminieren geteilte Geheimnisse für menschliche Authentifizierung. Kurzlebige Tokens und zertifikatsbasierte Authentifizierung übernehmen die Maschine-zu-Maschine-Kommunikation. Die Rolle eines Passwortmanagers entwickelt sich entsprechend weiter — von einem Tresor, der Passwörter speichert, zu einer Identitätsinfrastruktur-Schicht, die den vollständigen Lebenszyklus der Anmeldedaten verwaltet, einschließlich der Übergangszeit, in der Passwörter, Passkeys und Secrets koexistieren.
Organisationen, die diese Infrastruktur jetzt aufbauen, sind besser für diesen Übergang positioniert.
Fazit: Die Infrastruktur vor dem Breach aufbauen

Enterprise-Passwortmanagement ist Infrastruktur, kein Produktkauf. Organisationen, die es als solche behandeln — investieren in ordnungsgemäße Deployment-Architektur, phasenweise Implementierung und laufende Governance — vermeiden die durchschnittlichen Breach-Kosten von 4,44 Millionen USD, anstatt dazu beizutragen.
Das Entscheidungsframework ist unkompliziert: Bewertung der Datenresidenz-Anforderungen, Mapping der bestehenden Identitätsinfrastruktur, Berücksichtigung nicht-menschlicher Anmeldedaten neben menschlichen und Auswahl eines Deployment-Modells, das zum regulatorischen Umfeld und zur betrieblichen Kapazität passt.
Passwork bietet On-Premise-, Cloud- und Hybrid-Deployment und kombiniert Passwortmanagement mit Secrets-Management in einer einzigen Plattform. Kostenlose Migrationsunterstützung und Enterprise-Grade-Implementierungssupport stehen Organisationen zur Verfügung, die von einer Legacy-Lösung wechseln.
Häufig gestellte Fragen

Was ist Enterprise-Passwortmanagement?
Enterprise-Passwortmanagement speichert, kontrolliert und prüft organisatorische Anmeldedaten zentral durch verschlüsselte Tresore, rollenbasierte Zugriffskontrollen und automatisierte Passwortrotation. Im Gegensatz zu Consumer-Tools bieten Enterprise-Lösungen IT-Überwachung, Compliance-Berichte und Integration mit bestehender Identitätsinfrastruktur.
Wie unterscheidet sich Enterprise-Passwortmanagement von einem regulären Passwortmanager?
Enterprise-Lösungen fügen zentralisierte Administration, vollständige Audit-Protokollierung und Identity-Provider-Integration mit AD/LDAP/SSO hinzu. Sie bieten Deployment-Flexibilität — On-Premise, Cloud oder Hybrid — und übernehmen Secrets-Management für DevOps-Teams, nicht nur individuelle Passwortspeicherung.
Welches Deployment-Modell ist das richtige für meine Organisation?
Regulierte Branchen erfordern typischerweise On-Premise-Deployment für Datensouveränität. Verteilte Belegschaften mit begrenzten IT-Ressourcen profitieren von Cloud-Deployment. Multinationale Unternehmen mit variierenden regionalen Vorschriften nutzen oft Hybrid-Architekturen, die sensible Anmeldedaten On-Premise halten, während Cloud-Zugriff auf die allgemeine Belegschaft erweitert wird.
Wie unterstützt Enterprise-Passwortmanagement die Compliance mit GDPR, HIPAA und PCI DSS?
Audit-Protokollierung dokumentiert jedes Zugriffsereignis auf Anmeldedaten und erfüllt Dokumentationsanforderungen gemäß GDPR Artikel 30, HIPAAs Zugriffskontroll-Standards und PCI DSS Anforderung 8. Automatisierte Passwortrichtlinien-Durchsetzung demonstriert Kontrollen, und On-Premise-Deployment unterstützt Datenresidenz-Verpflichtungen.
Was ist Zero-Knowledge-Architektur und warum ist sie wichtig?
Zero-Knowledge bedeutet, dass alle Ver- und Entschlüsselung auf dem Gerät des Benutzers stattfindet. Der Anbieter hält niemals Klartext-Anmeldedaten oder die Schlüssel zu deren Entschlüsselung. Selbst im Falle einer anbieterseitigen Sicherheitsverletzung würden Angreifer nur Chiffretext abrufen.
Wie verarbeitet ein Enterprise-Passwortmanager Servicekonten und API-Schlüssel?
Dedizierte Secrets-Management-Funktionen speichern API-Schlüssel, Datenbank-Verbindungsstrings, Zertifikate und Servicekonto-Anmeldedaten neben menschlichen Passwörtern. Automatisierte Rotation integriert sich mit Deployment-Pipelines, und Just-in-Time-Injection liefert Anmeldedaten im Moment des Bedarfs an Systeme, ohne sie im Klartext preiszugeben.

Enterprise-Passwortverwaltung: Umfassender Leitfaden für B2B-Organisationen
Ein umfassender Leitfaden zur Enterprise-Passwortverwaltung für B2B-Entscheider. Deployment-Optionen (Cloud, On-Premise, Hybrid), Sicherheitsarchitektur und Best Practices für die Implementierung.