Outdated password practices, such as memorizing credentials or enforcing complex rules, consistently fail against today's threats. The Verizon Data Breach Investigations 2025 Report reveals that compromised credentials remain the leading cause of security incidents, with 22% of hacking-related breaches leveraging stolen or weak passwords.
Credential stuffing accounts for up to 19% of daily authentication attempts in enterprise environments. At $4.4 million per incident, the average breach cost reported by IBM in 2025 shows what's at stake.
The evolution of password management
Over the past decade, password management has fundamentally changed. We have moved away from frustrating, outdated practices like mandatory monthly password changes. Today, frameworks like NIST SP 800-63 guide organizations toward a more practical approach: longer passphrases and multi-factor authentication (MFA).
Security used to rely on complexity for its sake. Modern policies focus on resilience against real-world threats. A long, memorable passphrase is now far more effective than a short password packed with arbitrary special characters. Because long passphrases are harder to crack using brute-force methods, and their convenience helps users avoid unsafe practices like writing down their passwords.
Core password management
Password management relies on secure passwords, password managers, and MFA. Password policies adhere to NIST SP 800-63 standard by emphasizing the use of strong passwords and the adoption of multifactor authentication (MFA). These policies effectively address the most common entry points attackers use. This approach ensures that credential storage complies with audit and regulatory requirements.
Password managers make it easier to store complex passwords and help organizations maintain consistent credential policies. They also include built-in MFA support, providing an additional layer of verification. As a result, even if a password is compromised, the account remains protected.
Implications and benefits for enterprises:
- Password managers are important for secure credential storage
- Multi-factor authentication (MFA) provides an additional layer of protection
- Password policies help maintain secure password hygiene across systems
- Password strength is a defense against attacks like credential stuffing
Creating reliable passwords
Secure passwords defend against brute-force attacks, but length matters more than complexity. For accounts without MFA, NIST SP 800-63B sets the minimum password length to 8 characters, and with MFA to 15 characters.
Composition rules (uppercase, numbers, symbols) are now explicitly forbidden — they lead to predictable patterns like "P@ssw0rd567". Instead, encourage passphrases. Random word combinations like "correct-horse-battery-staple" are harder to crack than short complex strings.
Characteristics of secure passwords:
- Length: at least 12 characters
- Complexity: random letters, numbers, symbols
- Memorability: use passphrases
The role of password managers
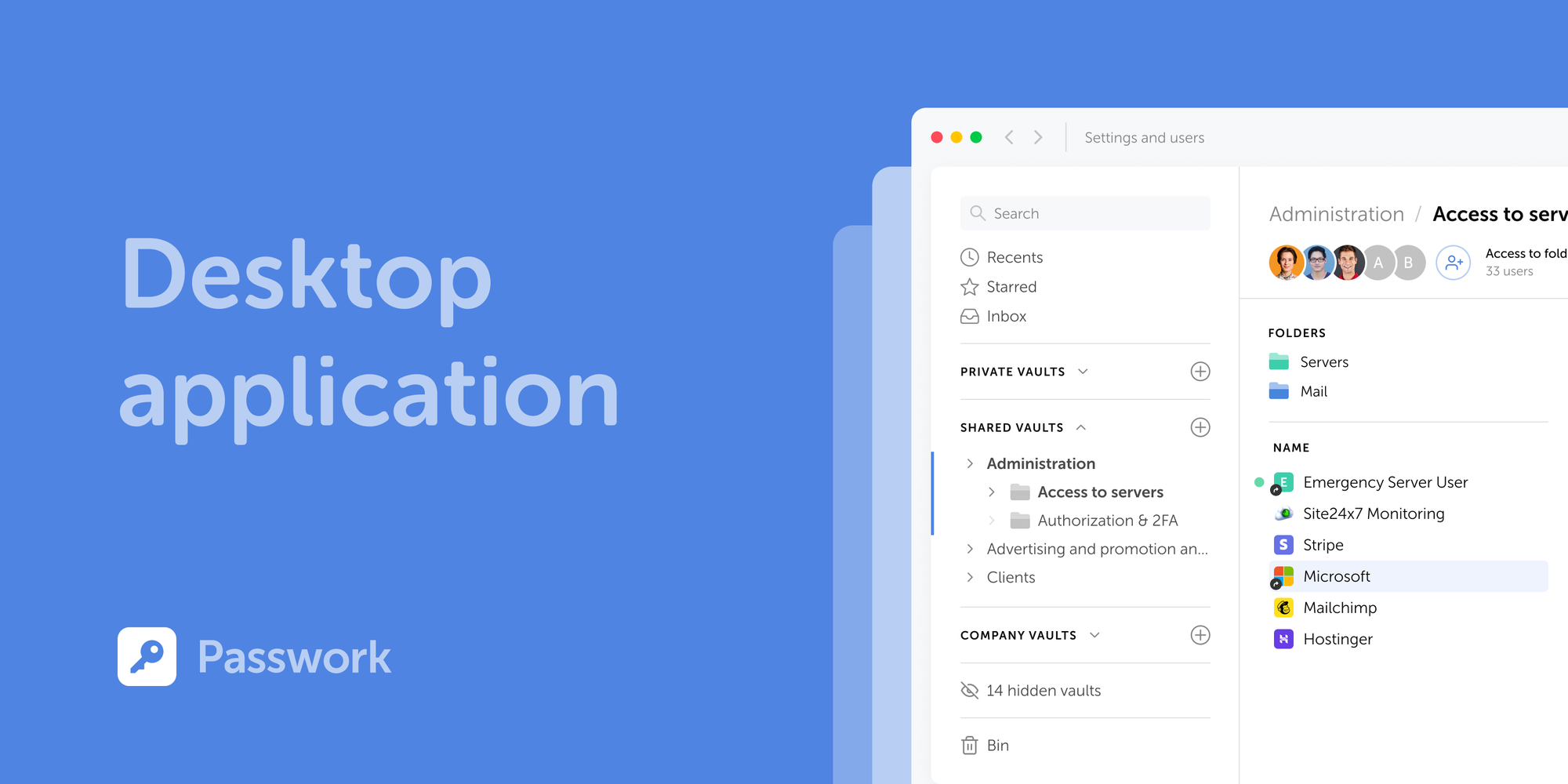
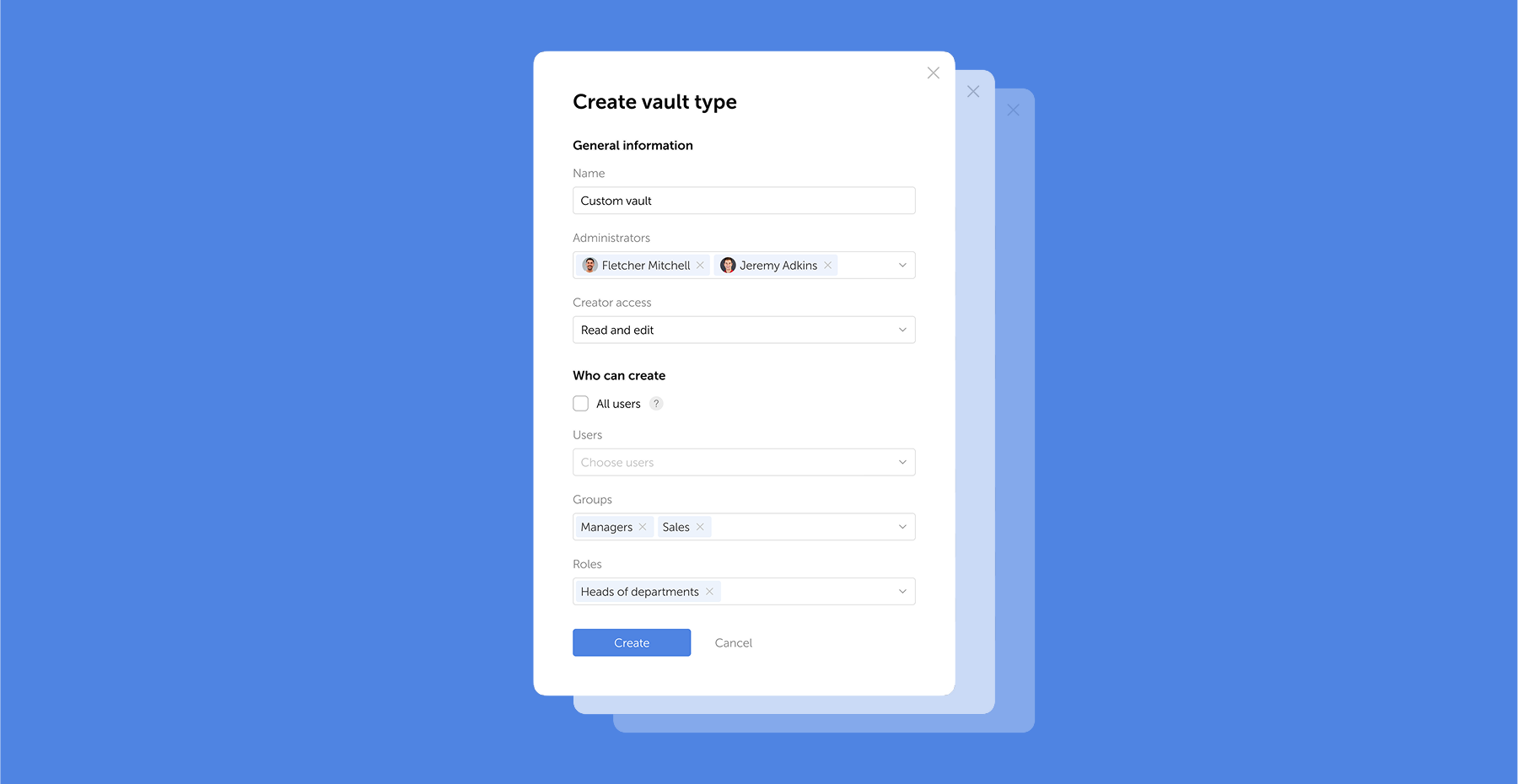
Behind the scenes, enterprise password managers handle encryption and authentication in addition to credential storage. With zero-knowledge architecture, the data stays encrypted on your device, and the provider never sees it. When selecting the right solution, it’s important to focus on key features that ensure security and adaptability: strong encryption, flexible deployment (cloud or on-premise), and built-in MFA support.
Some compliance and security policies call for keeping data behind a company's own firewall. For these organizations, on-premise deployment is a hard requirement. Passwork supports both cloud and on-premise, so you can choose what fits your infrastructure.
Multi-factor authentication: Security multiplier
MFA remains necessary for account protection — the DBIR treats it as a baseline. Yet the report also warns against complacency. Token theft, adversary-in-the-middle attacks, where an attacker intercepts communication between the user and the server, and SIM swapping are already identified as MFA bypass techniques in the 2025 dataset, and these threats are expected to become even more prevalent in the future.
Phishing-resistant methods like FIDO2 / WebAuthn offer stronger defense by binding credentials cryptographically to specific domains and devices.
Steps to implement MFA across common platforms:
- Enable MFA for all user accounts
- Choose your MFA method (SMS, app, or hardware token)
- Integrate with existing identity management systems (AD / LDAP / SSO)
- Set up recovery options for lost authentication factors
- Educate users on MFA use and benefits
Avoiding password reuse and its dangers
Credential stuffing exploits password reuse at scale. Credentials leaking from one site often lead attackers to test them across others, where they succeed in 0.2–2% of attempts. With billions of stolen credentials available, attackers can compromise thousands of accounts.
Password managers solve this — they generate unique passwords for every account. If a breach occurs on one platform, it remains contained and cannot spread to other systems.
Key practices to prevent password reuse:
- Use unique passwords for all accounts
- Store them securely in a password manager
- Regularly update password policies
When you evaluate password managers, deployment flexibility matters. For organizations with compliance requirements or existing infrastructure, it can be a deciding factor. Both cloud and on-premise options are available for testing in a demo environment that matches your actual setup.
Enterprise password management best practices

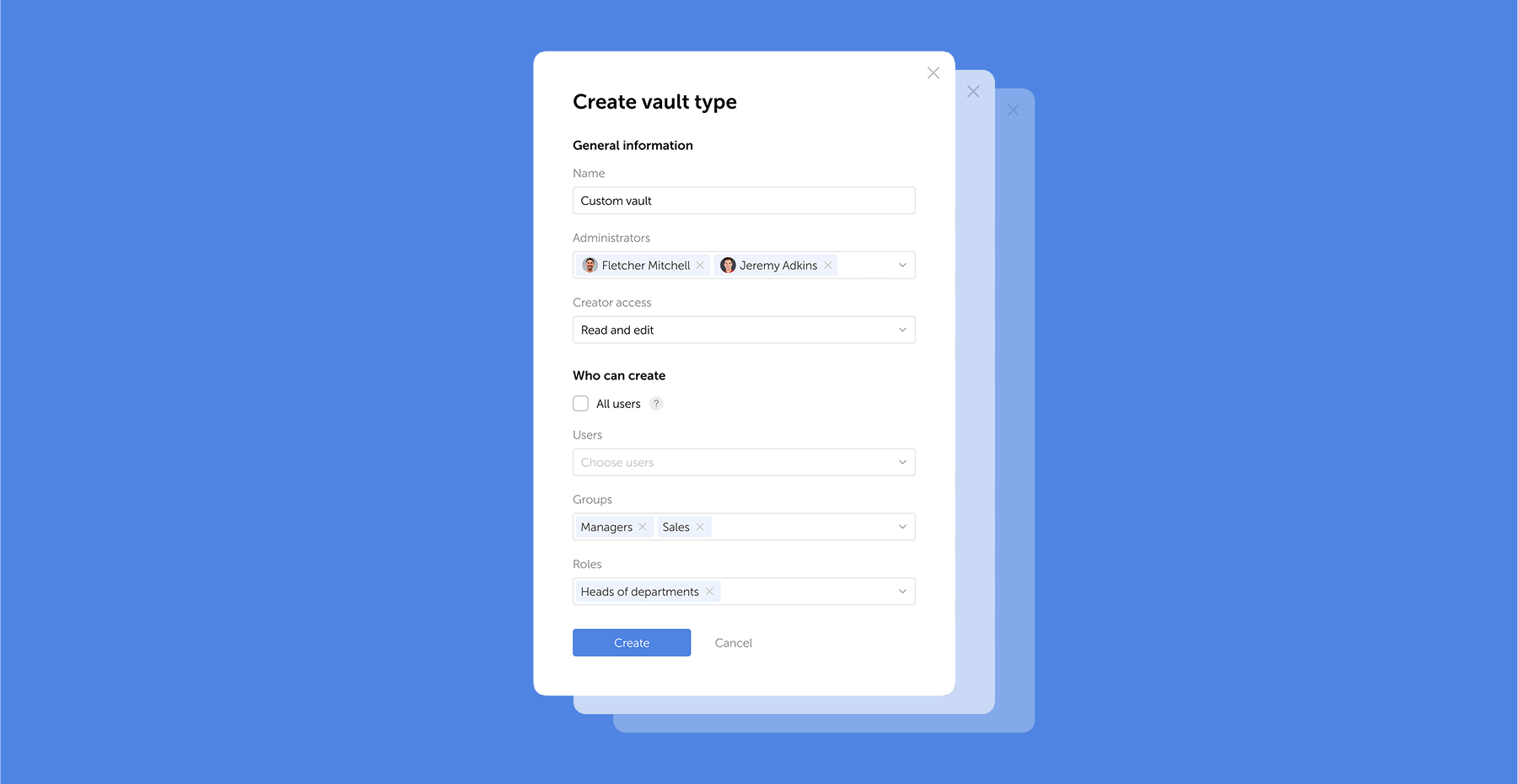
At the organizational level, password management has to account for team hierarchies, distributed infrastructure, and compliance rules. Centralized management, policy enforcement, and integration with existing systems reduce the risk of credential-related breaches. For privileged accounts, this extends to privileged access management (PAM) controls, limiting who can access critical systems and how.
Given the moderate to high implementation complexity (3-6 months), organizations should set realistic expectations. A successful enterprise-level strategy includes the use of password managers with multi-factor authentication, alongside solid password policies that follow current security standards.
Implementing centralized password management solutions
Before you select an enterprise password management system, evaluate deployment options: cloud, on-premises, or both, against your organization's size, security needs, and compliance rules.
A centralized platform applies password policies consistently across all users and removes the risk of employees skipping rules or using unapproved workarounds. For secure credential management, pair your password manager with multi-factor authentication.
Password policies that balance security and usability
Without proactive monitoring, suspicious login patterns can go unnoticed for weeks or months. To detect credential stuffing, which the Verizon DBIR identifies as an increasingly prevalent attack type, security teams rely on behavioral analysis and rate limiting. For brute-force attacks, account lockout policies act as the primary countermeasure.
To block brute force attacks, security teams rely on account lockout and rate limiting. By establishing baseline login patterns and setting deviation alerts, organizations can spot anomalies early. Regular reviews of password policies against actual login data reveal where rules create friction without adding security. Quick responses to emerging risks keep systems protected.
Advanced strategies beyond passwords
Passwordless authentication replaces traditional passwords with more secure methods. Instead of typed credentials, WebAuthn uses biometrics or security tokens. Because credentials never leave the device, phishing and credential theft no longer apply.
According to NIST SP 800-63B, hardware-bound implementations, such as FIDO2 security keys, can meet AAL3, the highest authenticator assurance level. Synced passkeys satisfy AAL2 requirements.
Beyond eliminating passwords, these methods improve user experience and align with NIST's push for stronger authentication. Organizations should keep MFA in place during the transition. MFA continues to protect accounts while passwordless adoption scales across the organization.
The path to passwordless authentication
With WebAuthn, biometrics or security tokens replace passwords using public-key cryptography. When paired with hardware-bound keys, this method meets NIST highest assurance level (AAL3) for identity verification. All major browsers support WebAuthn today, though implementation complexity varies. A gradual approach works best: start with MFA for layered security, then introduce passwordless authentication step by step.
Recommended steps for transitioning to passwordless authentication:
- Assess the current MFA implementation. Verify that MFA is configured to provide an extra layer of protection.
- Integrate WebAuthn. Implement WebAuthn, use biometrics or security tokens.
- Educate users. Prepare your team with proper training on the new authentication methods.
- Update security policies. Revise security policies to reflect the technology integration.
- Monitor and evaluate. Continuously track and evaluate the effectiveness of passwordless authentication.
Operational metrics for password management
Without clear metrics, password management stays invisible to leadership. Tracking specific indicators helps demonstrate their value across the organization. Start with these metrics: help desk ticket volume for password resets, MFA adoption rates, time to detect anomalous login attempts, and password reuse rates per department.
Beyond operational metrics, security standards like GDPR, HIPAA, and PCI DSS require organizations to verify compliance through audit trails — something centralized password management automatically provides. Regular reporting on these metrics turns security from a cost center into a documented, accountable program.
Building a culture of password security
Cybercrime increasingly targets human behavior. Technical controls alone cannot close this gap. Across the organization, strong password habits reduce risk more than any single tool.
Long-term adoption depends on combining sound password practices with security awareness. Employees need to understand why MFA matters and how to spot phishing attempts. When security becomes part of the daily workflow, adoption follows naturally.
Transfer your remaining subscription period and enjoy 20% off your first renewal.
Frequently Asked Questions

What are the important password management best practices for 2026?
For 2026, password management practices include using unique passwords for every account, leveraging password managers for secure storage, and implementing multi-factor authentication (MFA) for added protection. Organizations should adopt a centralized password policy and maintain security awareness to protect against threats, such as credential stuffing.
How do password managers improve security compared to manual password management?
Password managers improve security by storing encrypted credentials, generating secure passwords, and preventing password reuse. Unlike manual management, password managers automate password updates and integrate with multi-factor authentication (MFA), boosting overall security and minimizing human error, which can lead to breaches.
Why is implementing multi-factor authentication important for password security?
Implementing multi-factor authentication (MFA) adds an important layer of security by requiring users to provide more than just a password. Even if passwords are compromised, MFA protects accounts by validating identity through additional verification methods such as security tokens or biometric authentication, reducing the risk of unauthorized access.
How should organizations balance security requirements with user experience in password management?
Organizations should implement user-friendly password policies that encourage reliable passwords while integrating multi-factor authentication to improve security without complicating the user experience. Password managers simplify password management, so users can follow protocols without sacrificing convenience. Balancing usability and security is needed for compliance and user adoption.
What are the risks of password reuse, and how can they be mitigated?
Password reuse increases the risk of credential stuffing attacks, where attackers use compromised credentials to gain unauthorized access to multiple accounts. Password managers mitigate this risk: they generate and store unique passwords for each account, prevent reuse across platforms, and limit the number of systems exposed if one credential leaks.

Password management best practices for enterprise security
Cybercrime increasingly targets human behavior. Technical controls alone cannot close this gap. Across the organization, strong password habits reduce risk more than any single tool.